Privacy and data protection
-
News
14 May 2026

BlackBerry doubles down on secure communications
Having sold its Cylance endpoint security portfolio to Arctic Wolf, the former smartphone pioneer is doubling down on military-grade encryption and post-quantum cryptography to shield critical infrastructure from AI-driven threats Continue Reading
By- Aaron Tan, Informa TechTarget
-
News
05 May 2026

CSA: Take AI cyber threats to the boardroom
Current cyber risk assumptions may no longer be valid given the speed of advanced AI, warns the chief executive of Singapore’s Cyber Security Agency Continue Reading
By- Aaron Tan, Informa TechTarget
-
News
20 Jun 2024

Sir Alan Bates hits out at Post Office ‘incompetence’ after data breach
Victims of the scandal react with anger at news the Post Office published a document containing their names and addresses on its website Continue Reading
By- Karl Flinders, Chief reporter and senior editor EMEA
- Bryan Glick, Editor in chief
-
News
19 Jun 2024

Microsoft admits no guarantee of sovereignty for UK policing data
Documents show Microsoft’s lawyers admitted to Scottish policing bodies that the company cannot guarantee sensitive law enforcement data will remain in the UK, despite long-standing public claims to the contrary Continue Reading
By- Sebastian Klovig Skelton, Data & ethics editor
-
Definition
12 Jun 2024

privacy impact assessment (PIA)
A privacy impact assessment (PIA) is a method for identifying and assessing privacy risks throughout the development lifecycle of a program or system. Continue Reading
By- Cameron Hashemi-Pour, Former Site Editor
- Paul Kirvan
- Ben Cole, Executive Editor
-
News
11 Jun 2024

PSNI ran secret unit to monitor journalists’ and lawyers’ phones, claims former senior officer
The Police Service of Northern Ireland denies claims that its anti-corruption unit used a standalone computer to ‘avoid scrutiny and control’ Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
10 Jun 2024

NHS blood stocks running low after ransomware attack
The NHS is appealing for people with O Positive and O Negative blood types to come forward to donate as hospitals in London struggle to keep critical services running after ransomware attack Continue Reading
By- Alex Scroxton, Security Editor
-
News
07 Jun 2024

Northern Irish police used covert powers to monitor over 300 journalists
PSNI publishes report on police surveillance of journalists and lawyers, but Northern Ireland’s Policing Board says it does not give the assurances needed Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
07 Jun 2024

DDoS gang threatens to disrupt European elections
Russian hacktivists are threatening to disrupt the European Parliament elections, while the BBC reports on new deepfake threats to the UK’s electoral process Continue Reading
By- Alex Scroxton, Security Editor
-
News
07 Jun 2024

Bitdefender makes MDR services free to NHS bodies hit by Qilin
Bitdefender offers NHS bodies affected by a major cyber incident free access to its product suite, as the health service continues to deal with the impact of the Qilin ransomware attack on partner Synnovis Continue Reading
By- Alex Scroxton, Security Editor
-
News
07 Jun 2024

Sophos uncovers Chinese state-sponsored campaign in Southeast Asia
Sophos found three distinct clusters of activity targeted at a high-level government organisation that appeared to be tied to Chinese interests in the South China Sea Continue Reading
By- Aaron Tan, Informa TechTarget
-
News
06 Jun 2024

FBI finds 7,000 LockBit decryption keys in blow to criminal gang
The US authorities say they now have more than 7,000 LockBit decryption keys in their possession and are urging victims of the prolific ransomware gang to come forward Continue Reading
By- Alex Scroxton, Security Editor
-
News
05 Jun 2024

Qilin ransomware gang likely behind crippling NHS attack
Security experts investigating a major cyber attack on an NHS partner that has caused frontline services across South London to grind to a halt say the Qilin ransomware gang appears to be the culprit Continue Reading
By- Alex Scroxton, Security Editor
-
News
04 Jun 2024

OAIC files civil penalty action against Medibank
The OAIC alleges that Medibank failed to take reasonable steps to protect the personal information of 9.7 million Australians in the October 2022 data breach Continue Reading
By- Aaron Tan, Informa TechTarget
-
News
04 Jun 2024

Invasive tracking ‘endemic’ on sensitive support websites
Websites set up by police, charities and universities to help people get support for sensitive issues like addiction and sexual harassment are deploying tracking technologies that harvest information without proper consent Continue Reading
By- Sebastian Klovig Skelton, Data & ethics editor
-
News
04 Jun 2024

NHS services at major London hospitals disrupted by cyber attack
A major cyber attack at NHS services provider Synnovis is disrupting frontline care at hospitals across London Continue Reading
By- Alex Scroxton, Security Editor
-
News
04 Jun 2024
Russia used fake AI Tom Cruise in Olympic disinformation campaign
Microsoft threat researchers report a surge in Russian disinformation campaigns targeting the 2024 Summer Olympics, including AI-enhanced propaganda Continue Reading
By- Alex Scroxton, Security Editor
-
News
03 Jun 2024

Police chief commissions ‘independent review’ of surveillance against journalists and lawyers
PNSI chief constable appoints lawyer to conduct review into police phone surveillance of journalists, lawyers and NGOs Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
03 Jun 2024

Major breaches allegedly caused by unsecured Snowflake accounts
Significant data breaches at Ticketmaster and Santander appear to have been orchestrated through careful targeting of the victims’ Snowflake cloud data management accounts Continue Reading
By- Alex Scroxton, Security Editor
-
News
03 Jun 2024

Sellafield local authority slammed over response to North Korean ransomware attack
The local authority for Europe’s biggest nuclear site has been slammed by auditors for its response to a North Korea-linked cyber attack that temporarily crippled its operations Continue Reading
By -
News
02 Jun 2024

Ticketek Australia hit by data breach
Customer names, dates of birth and email addresses of Ticketek Australia account holders reportedly impacted in latest data breach affecting event ticketing firm Continue Reading
By- Aaron Tan, Informa TechTarget
-
News
31 May 2024

Law student ‘unfairly disciplined’ after reporting data breach blunder
A law student has accused a leading legal college of unethical behaviour and a “lack of integrity” after it brought misconduct proceedings against him when he reported a data security blunder Continue Reading
By -
News
29 May 2024

Storebrand divests from IBM over supply of biometrics to Israel
Norwegian asset manager Storebrand’s decision to divest from IBM comes amid growing scrutiny of the role technology companies play in Israel’s human rights abuses Continue Reading
-
News
29 May 2024

Proofpoint exposes AFF scammers’ piano gambit
Ransomware and nation state actors dominate the headlines, but fraud and scams still net career cyber criminals thousands from unsuspecting members of the public. Proofpoint reports on a campaign targeting victims of a musical inclination Continue Reading
By- Alex Scroxton, Security Editor
-
News
29 May 2024

Organisations value digital trust, but aren’t working at it
Three quarters of organisations believe digital trust is relevant to their businesses, yet clear gaps in strategies still seem to persist Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
29 May 2024

AI governance needs global approach
Doreen Bogdan-Martin, Secretary-General of the UN agency, International Telecommunication Union (ITU) argues that AI governance needs a world-wide approach Continue Reading
By- Doreen Bogdan-Martin
-
News
29 May 2024

Interview: EU data chief Ulrich Ahle on obstacles to Europe’s digital single market
EU data scheme Gaia-X is trying to plug the UK into Europe’s planned digital single market as opposition mounts to efforts to extend the reach of Europe’s vast and controversial data laws over global supply chains Continue Reading
By -
News
28 May 2024

Executive Interview: Why Dell wants to be your one-stop AI shop
At Dell Technologies World in Las Vegas, artificial intelligence was the talk of the town as Dell staked out an all-encompassing strategy ahead of an anticipated goldrush. Dell’s Nick Brackney explains why the tech giant believes it's onto a winner Continue Reading
By- Alex Scroxton, Security Editor
-
News
24 May 2024

Parliamentarians warn of UK election threat from Russia, China and North Korea
Joint parliamentary security committee chair Margaret Beckett writes to prime minister urging government to prepare for foreign states interfering with 4 July election Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
23 May 2024

Northern Ireland police face £750,000 fine after data protection blunder put lives at risks
Information commissioner John Edwards uses discretion to reduce proposed fine from £5.6m to £750,000 Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
21 May 2024

The Security Interviews: What is the real cyber threat from China?
Former NCSC boss Ciaran Martin talks about nation-state attacks, why the UK has become so exercised about cyber espionage, and how our leaders are in danger of misunderstanding their adversaries Continue Reading
By- Alex Scroxton, Security Editor
-
News
20 May 2024

WikiLeaks founder Julian Assange granted appeal
Two high court judges granted WikiLeaks founder Julian Assange leave to appeal against extradition to the US after defence lawyers argued that the US had failed to give adequate assurances Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
15 May 2024

US authorities crack BreachForums for a second time
The BreachForums data leak website has been seized by the FBI and international partners again Continue Reading
By- Alex Scroxton, Security Editor
-
News
15 May 2024

GCHQ to protect politicians and election candidates from cyber attacks
The National Cyber Security Centre, part of GCHQ, to protect election candidates from hostile state cyber attacks Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
14 May 2024

NHS trust dismisses governors who questioned allegations of email tampering
Two NHS trust governors who raised questions in a dispute over allegations of email tampering concerning whistleblower Peter Duffy have been dismissed after an investigation that followed their suspension Continue Reading
By -
News
10 May 2024

Major breach of customer information developing at Dell
Almost 50 million data records relating to Dell customers appear to have been compromised in a major cyber breach Continue Reading
By- Alex Scroxton, Security Editor
-
News
10 May 2024

Over 5.3 billion data records exposed in April 2024
The number of data records breached in April 2024 hit over five billion, a staggering year-on-year increase Continue Reading
By- Alex Scroxton, Security Editor
-
News
09 May 2024

Cyber attack victims need to speak up, says ICO
The Information Commissioner’s Office is urging organisations to be transparent and learn from each other’s mistakes as it reveals most of the cyber attacks it responds to stem from the same core errors Continue Reading
By- Alex Scroxton, Security Editor
-
News
09 May 2024
Ofcom publishes draft online child safety rules for tech firms
In the draft codes, Ofcom calls on technology firms to use ‘robust’ age-checking and content moderation systems to keep harmful material away from children online Continue Reading
By- Sebastian Klovig Skelton, Data & ethics editor
-
News
08 May 2024

Police accessed phone records of ‘trouble-making journalists’
The Police Service of Northern Ireland ran a rolling programme to monitor phone records of journalists to identify the source of police leaks, it was claimed today Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
08 May 2024

Germany: European Court of Justice ruling on EncroChat could lead to new legal challenges
A ruling by the European Court of Justice could prompt legal challenges in EncroChat prosecutions in Germany and other EU states Continue Reading
By- Bill Goodwin, Investigations Editor
-
Opinion
07 May 2024
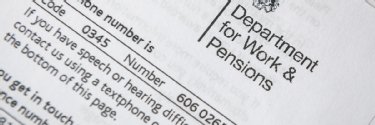
Government plans to scan bank accounts of disabled people will lead to another scandal
The government is sleepwalking into another scandal as it pushes plans for ‘bank scanning’ algorithms to monitor bank accounts of disabled people Continue Reading
By- Mikey Erhardt, campaigner at Disability Rights UK
-
News
07 May 2024

Chinese APT suspected of Ministry of Defence hack
A cyber attack on the Ministry of Defence is suspected to be the work of threat actors working on behalf of Chinese intelligence Continue Reading
By- Alex Scroxton, Security Editor
-
Feature
07 May 2024

What does the Data Protection and Digital Information Bill mean for UK industry?
The Data Protection and Digital Information Bill is the first shift in the UK’s data protection regime since leaving the EU, but what could it mean for UK industry? Continue Reading
-
News
03 May 2024

EU calls out Fancy Bear over attacks on Czech, German governments
The European Union, alongside member states Czechia and Germany, have accused Russian government APT Fancy Bear of being behind a series of attacks on political parties and government bodies Continue Reading
By- Alex Scroxton, Security Editor
-
News
03 May 2024

Why IAM is central to cyber security
BeyondTrust’s chief security strategist talks up the importance of identity and access management, and the role of cyber insurance in driving security improvements Continue Reading
-
News
02 May 2024

Dropbox Sign user information accessed in data breach
Account data belonging to Dropbox Sign users was accessed by an unknown threat actor after they hacked into the organisation’s backend infrastructure Continue Reading
By- Alex Scroxton, Security Editor
-
News
02 May 2024

BBC instructs lawyers over allegations of police surveillance of journalist
Lawyers for the BBC have written to the Investigatory Powers Tribunal over allegations that the Police Service of Northern Ireland spied on investigative journalist Vincent Kearney Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
01 May 2024

Australia’s Qantas apologises for mobile app data breach
Australian flag carrier Qantas has apologised after a glitch in its mobile application temporarily enabled some customers to view the flights and booking details of other frequent fliers on two separate occasions Continue Reading
By- Alex Scroxton, Security Editor
-
News
01 May 2024
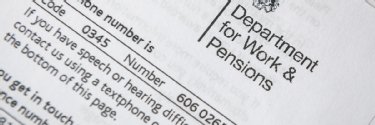
DWP anti-fraud measures will allow monitoring of bank accounts of landlords, carers and parents
Parliamentarians raise concerns that a proposed law to require banks to monitor the accounts of millions of people receiving state benefits could lead to those on welfare being denied accommodation or bank accounts Continue Reading
By- Bill Goodwin, Investigations Editor
-
Opinion
01 May 2024

Are we ready for the era of the ‘sentient’ document?
This year is set to be the automation of documents since the invention of the printing press. Content control is key Continue Reading
By- John Bates
-
News
01 May 2024

Autonomous weapons reduce moral agency and devalue human life
Military technology experts gathered in Vienna have warned about the detrimental psychological effects of AI-powered weapons, arguing that implementing systems of algorithmic-enabled killing dehumanises both the user and the target Continue Reading
By- Sebastian Klovig Skelton, Data & ethics editor
-
News
30 Apr 2024

Persistent data breaches deny people with HIV dignity and privacy
The ICO has urged charities and healthcare organisations that work with people living with HIV to do better when it comes to protecting their personal data, after the HIV status of more than 100 people was accidentally disclosed by London’s Central YMCA Continue Reading
By- Alex Scroxton, Security Editor
-
News
25 Apr 2024

Zero trust is a strategy, not a technology
Zero-trust security should be seen as a strategy to protect high-value assets and is not tied to a specific technology or product, says the model’s creator John Kindervag Continue Reading
By- Aaron Tan, Informa TechTarget
-
News
24 Apr 2024

TikTok ban sails through US Senate
A law that will ban TikTok in the US unless its owner sells up pronto passed the US Senate by a landslide majority after being included in a package of military aid Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
23 Apr 2024

Questions for IT and cyber leaders from the CSRB Microsoft report
The US government's CSRB report on last year's state sponsored cyber attacks on Microsoft raises significant concerns for Redmond and its customers. Expert Owen Sayers outlines five key questions IT and cyber security leaders should now consider Continue Reading
By- Owen Sayers, Secon Solutions
-
News
22 Apr 2024

Former Sellafield consultant claims the nuclear complex tampered with evidence
Whistleblower Alison McDermott claims former employer Sellafield tampered with metadata in letters used in evidence during an employment tribunal Continue Reading
By- Tommy Greene
- Bill Goodwin, Investigations Editor
-
News
22 Apr 2024

Fujifilm plans to ‘make tape easy’ with Kangaroo SME appliance
Fujifilm to add 100TB SME-focused Kangaroo tape infrastructure in a box to existing 1PB offer, as energy efficiency and security of tape make it alluring to customers Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
News
21 Apr 2024

Crime agency criticises Meta as European police chiefs call for curbs on end-to-end encryption
Law enforcement agencies step up demands for ‘lawful access’ to encrypted communications Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
19 Apr 2024

Report reveals Northern Ireland police put up to 18 journalists and lawyers under surveillance
Disclosures that the Police Service of Northern Ireland obtained phone communications data from journalists and lawyers leads to renewed calls for inquiry Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
19 Apr 2024

Tech companies operating with opacity in Israel-Palestine
Tech firms operating in Occupied Palestinian Territories and Israel are falling “woefully short” of their human rights responsibilities amid escalating devastation in Gaza, says Business & Human Rights Resource Centre Continue Reading
By- Sebastian Klovig Skelton, Data & ethics editor
-
News
18 Apr 2024

CSA warns of emerging security risks with cloud and AI
Few users appreciate the security risks of cloud and have the expertise to implement the complex security controls, says CSA chief executive David Koh Continue Reading
By- Aaron Tan, Informa TechTarget
-
News
18 Apr 2024

TUC publishes legislative proposal to protect workers from AI
Proposed bill for regulating artificial intelligence in the UK seeks to translate well-meaning principles and values into concrete rights and obligations that protect workers from systems that make ‘high-risk’ decisions about them Continue Reading
By- Sebastian Klovig Skelton, Data & ethics editor
-
News
16 Apr 2024

US provides assurances over extradition of WikiLeaks founder Julian Assange
Extradition of the WikiLeaks founder moves a step closer after the US government gives diplomatic assurances over his treatment in the US. Assange supporters accuse the US of ‘weasel words’ Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
16 Apr 2024

CISOs not yet convinced to invest in AI
CISOs say their eyes are fixed firmly on threats like ransomware and supply chain attacks, and while AI is becoming a threat that needs to be dealt with, it’s not yet an immediate spending priority Continue Reading
By- Alex Scroxton, Security Editor
-
News
16 Apr 2024

CW Innovation Awards: Balancing security and user experience
The National University of Singapore’s Safe initiative has strengthened the security of IT systems and end-user devices while prioritising user experience through passwordless access Continue Reading
By -
Opinion
16 Apr 2024

2024 election security: Confronting disinformation and deepfakes
Although disinformation and deepfakes are a threat to electoral integrity, we already have ways to counter emerging threats and there is an opportunity is to adapt and scale these approaches to counter the challenge to democracy, writes Saj Huq. Continue Reading
By- Saj Huq, Plexal
-
Opinion
15 Apr 2024

Threat actors look to stolen credentials
In 2023, threat actors wrought havoc on corporate networks by logging in through valid accounts, and as bad actors begin investing in AI to help them identify priority targets, this problem is only expected to worsen in the future Continue Reading
By- Martin Borrett
-
News
15 Apr 2024

EU’s AI Act fails to protect the rule of law and civic space
Analysis reveals that the AI Act is ‘riddled with far-reaching exceptions’ and its measures to protect fundamental rights are insufficient Continue Reading
By- Josh Osman, Computer Weekly
-
News
12 Apr 2024

Apple iPhone security alert renews spyware concerns
An Apple security alert received by users in 92 countries raises fresh fears over ongoing campaigns by users of mercenary spyware products Continue Reading
By- Alex Scroxton, Security Editor
-
Feature
12 Apr 2024

5G networks and biometric breakthroughs: Navigating opportunities and risks
Businesses are quickly adopting 5G to introduce advanced security features such as facial recognition, but while these technologies improve safety and ease of use, they also raise concerns about how sensitive biometric information is gathered and may be misused Continue Reading
By -
News
12 Apr 2024

Executive interview: Balancing AI with human creativity
We speak to the chief product officer at Getty Images and iStock about the role generative AI can play in the image-making process. Continue Reading
By- Cliff Saran, Managing Editor
-
Feature
12 Apr 2024

European Digital Identity Wallet: One ID for EU citizens
The European Digital Identity Wallet is a personal digital wallet with which you will be able to identify yourself digitally in the future. Is this the solution for a centralised ID? Continue Reading
-
News
11 Apr 2024

Facial recognition to play key role in UK shoplifting crackdown
UK government will fund roll-out of police facial recognition across the country as part of its crackdown on shoplifting and violence against retail staff, but civil society groups say the government is attempting to police its way out of the cost-of-living crisis Continue Reading
By- Sebastian Klovig Skelton, Data & ethics editor
-
News
11 Apr 2024

Government dismisses Lords’ concerns over facial recognition
UK government is claiming police forces’ use of live facial recognition is comprehensively covered by existing laws, in response to a Lords investigation that found police lacked a clear legal basis to deploy it Continue Reading
By- Sebastian Klovig Skelton, Data & ethics editor
-
News
10 Apr 2024

Breakthrough may herald secure home quantum computing
An emerging approach to quantum security dubbed blind quantum computing may one day help spur mass adoption of quantum computing safely and securely, using technology that is already available today Continue Reading
By- Alex Scroxton, Security Editor
-
News
10 Apr 2024

Biden considering whether to end prosecution of WikiLeaks founder Julian Assange
US president Joe Biden says he is considering requests by Australia to end the prosecution of WikiLeaks founder Julian Assange under espionage and computer fraud charges Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
10 Apr 2024

Salesforce helps customers establish bug bounty programmes
Salesforce has added new learning content to its Trailhead platform designed to help customers develop their own bug bounty programmes Continue Reading
By- Alex Scroxton, Security Editor
-
News
09 Apr 2024

Public worried by police and companies sharing biometric data
More than half of the British public do not feel comfortable with police forces sharing biometric data with the private sector, including facial recognition images, to tackle crimes such as shoplifting Continue Reading
By- Josh Osman, Computer Weekly
-
Answer
09 Apr 2024

How do companies protect customer data?
Companies can protect customer data through various technical tools and strategies, like authentication and encryption. But some types of data need more protection than others. Continue Reading
By- Sandra Mathis, Microsoft
-
News
09 Apr 2024

Is a cyber arms control treaty out of reach?
The world needs cyber arms control more than ever, but the challenges facing a multilateral agreement will be hard to surmount, according to researchers at Germany’s Digital Society Institute Continue Reading
By- Alex Scroxton, Security Editor
-
News
09 Apr 2024

Police forces check intelligence and criminal databases after errors discovered in O2 phone data
Criminal Bar Association calls for information about reliability of communications data used in criminal trials to be disclosed Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
09 Apr 2024

Greek government fined over AI surveillance in refugee camps
Greece’s Data Protection Authority has issued a €175,000 fine against the country’s migration ministry over its deployment of artificial intelligence-powered security systems in refugee camps after the watchdog’s investigation found ‘serious shortcomings’ with the roll-out Continue Reading
-
News
08 Apr 2024

UK vet network CVS hit by cyber attack
Operations at UK-based veterinary network CVS have been disrupted by a cyber incident of an as-yet undisclosed nature Continue Reading
By- Alex Scroxton, Security Editor
-
Feature
05 Apr 2024

Seven ways to be sure you can restore from backup
Backups are no good if you can’t restore from them. We look at key elements of backup restoration, including backup audits, RPOs and RTOs, and how and when to test backups Continue Reading
-
News
05 Apr 2024

China ramps up use of AI misinformation
Microsoft researchers have identified a growing pattern of AI-laced misinformation and political interference coming from Chinese threat actors Continue Reading
By- Alex Scroxton, Security Editor
-
News
04 Apr 2024

Changes needed for SOCs and CSIRTs, claims Dutch research institute
Cyber security specialists need a game-changer to keep up with their adversaries, who increasingly use automation and AI for their attacks Continue Reading
By- Kim Loohuis
-
News
04 Apr 2024

Obituary: Professor Ross Anderson, pioneer in security engineering and campaigner
Ross Anderson, a titan in the field of security engineering and campaigner for privacy and security, has passed away Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
29 Mar 2024

Organisations getting better at spotting identity fraud
As the barriers to committing identity fraud continue to drop, organisations should consider more sophisticated technical measures to successfully up their game, according to a report Continue Reading
By- Alex Scroxton, Security Editor
-
Definition
28 Mar 2024

sensitive information
Sensitive information is data that must be protected from unauthorized access to safeguard the privacy or security of an individual or organization. Continue Reading
By- Nick Barney, Technology Writer
-
News
28 Mar 2024

UK plc going backwards on cyber maturity, Cisco report claims
Fewer UK organisations believe their cyber security postures have reached a mature level than did so 12 months ago, as they struggle to keep up with new challenges and a fast-evolving threat landscape Continue Reading
By- Alex Scroxton, Security Editor
-
News
28 Mar 2024

Sellafield to be prosecuted over alleged cyber compliance failure
Sellafield Ltd, the organisation responsible for cleaning up and decommissioning the UK's largest nuclear waste site, is to be prosecuted over alleged cyber security failings dating back to 2019 Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
28 Mar 2024

Facial recognition endangers us all without a clear legal basis
Technology researcher Stephanie Hare outlines the growing danger of the UK’s failure to legalise and regulate facial recognition technology Continue Reading
-
News
27 Mar 2024

Ransomware gang leaks data stolen from Scottish NHS board
Data stolen from an earlier attack on NHS Dumfries and Galloway has been leaked by a ransomware gang that claims to be in possession of much more content Continue Reading
By- Alex Scroxton, Security Editor
-
News
26 Mar 2024

Qilin ransomware gang claims cyber attack on the Big Issue
A ransomware attack on the systems of publisher and social enterprise Big Issue Group has been claimed by the Qilin gang Continue Reading
By- Alex Scroxton, Security Editor
-
News
26 Mar 2024

WikiLeaks founder Julian Assange given temporary reprieve over extradition
Court seeks assurances from the US that Assange will be given First Amendment Rights, will not prejudiced at trial because of his nationality, and will not be subject to the death penalty Continue Reading
By- Bill Goodwin, Investigations Editor
- Sander Priston
-
News
26 Mar 2024

NCSC reaffirms guidance for those at risk of Chinese state hacking
As the UK and US governments announce sanctions and indictments of a Chinese state threat actor, the NCSC has reiterated its security advice for individuals at risk of being targeted for espionage purposes Continue Reading
By- Alex Scroxton, Security Editor
-
News
26 Mar 2024

US authorities charge seven over Chinese hacking
The US Department of Justice has charged seven Chinese nationals linked to the APT31 threat actor that targeted politicians in the UK and US Continue Reading
By- Alex Scroxton, Security Editor
-
News
25 Mar 2024

Which? calls for government action on fake banking sites
Amid high volumes of spoofed, fraudulent banking websites, Which? is calling for the government to implement new legal obligations for domain registrars Continue Reading
By- Alex Scroxton, Security Editor
-
News
25 Mar 2024

Chinese hackers responsible for two ‘malicious’ cyber campaigns against UK
Government sanctions two Chinese nationals and a Chinese company identified as responsible for cyber campaigns against government officials and members of parliament Continue Reading
By- Bill Goodwin, Investigations Editor
-
News
25 Mar 2024

Britain’s democracy under threat from Chinese cyber attackers, government warns
The deputy prime minister, Oliver Dowden, is due to tell Parliament that Beijing is behind a hacking attack that obtained details of 40 million UK voters and has targeted parliamentarians who have criticised the regime Continue Reading
By- Bill Goodwin, Investigations Editor
-
Tip
22 Mar 2024

Data protection impact assessment template and tips
Conducting a data protection impact assessment is key to evaluating potential risk factors that could pose a serious threat to individuals and their personal information. Continue Reading
By


