Latest News
-
Councils exit 10-year Capita deal to boost project velocity
Two councils that were once part of a five-council group outsourced to Capita take back control of their IT to allow for decision-making and IT projects that aren’t bound by the slowest member
-
Scale of Synnovis breach widens as Essex NHS Trust comes forward
Mid and South Essex NHS Foundation Trust has become the latest NHS body to confirm data on its patients were stolen in a 2024 ransomware attack on lab services partner Synnovis.
-
Partnership to ensure entry-level jobs for young people
Early Careers Jobs Alliance between the government and industry will provide skills and guidance to ensure young people can begin careers in an AI-focused world
-
Starmer announces sovereign compute strategy
Prime minister launches strategy to develop UK sovereign compute capability as government pumps £1.1bn into AI hardware plan
-
Red tape or responsible tech?
As artificial intelligence and digital regulations tighten across the UK and Europe, government technology suppliers are redesigning products and absorbing rising compliance costs, raising questions about regulatory impact
-
DfE proposes changes to student funding for assistive tech
The UK Department for Education is proposing to reduce access to paid-for assistive technology in favour of free-to-access services
In Depth
-
How AI is being used to manage networks
Network management is becoming reliant on artificial intelligence-enabled tools, which use machine learning based on network monitoring data
-
Scandinavia’s Kitron leans into AI but depends on ERP and local links to keep electronics production
Norway-headquartered Kitron Group is on a growth path and relies on local-market nous and partners
-
Sweden’s Hexagon takes a measuring tape to the industrial world… and its virtual counterpart
Stockholm-headquartered company is applying precision observability and digital twins to make a safer, more sustainable and efficient world
-
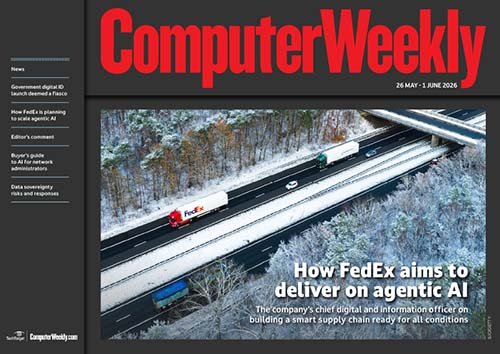
E-Zine | May 2026
How FedEx aims to deliver on agentic AI
Download -
E-Handbook | May 2026
Why real-time analytics is key to AI success
Download -
E-Zine | May 2026
CW APAC - Trend Watch: Agentic AI
Download -
E-Zine | May 2026
Generative AI is changing the game in video gaming
Download -
E-Zine | May 2026
Mastering a marathon with the future of healthtech
Download
Blogs
-
Pushing pilots-to-production: NTT DATA expands collaboration with Google Cloud - CW Developer Network
NTT DATA (hereafter NTT Data) wants software application developers to be able to go from pilot to production (not a branded or de facto industry term, but it should be) in the most fluid, ... Continue Reading
-
How the UK should take AI from sandboxes to scale- Data Matters
This is a guest blogpost by Rupal Karia, SVP & GM – UKI, Northern Europe & MEA at Celonis. As we enter London Tech Week, many conversations will be focused on how to make the UK a key ... Continue Reading
-
Harness tightens up AI ROI spend with new tools- CW Developer Network
Software delivery company Harness produced two new products recently. The directly-named AI DLC Insights and Cloud & AI Cost Management arrive with a promise of their ability to give software ... Continue Reading
-
Getting by with a little help from AI- Cliff Saran's Enterprise blog
A couple of weeks ago OpenAI announced that a prominent open problem central to combinatorial geometry, has been solved autonomously by AI. The planar unit distance problem, first posed by Paul ... Continue Reading
Opinion
-

Claude Mythos forces the conversation on defensive AI
The Computer Weekly Security Think Tank considers if Anthropic’s Claude Mythos frontier AI model is a benefit or barrier to achieving resilient enterprise IT security, and how security leaders need to adapt.
-

Tech bros beware - Erin Brockovich is coming for you
The campaigning heroine of the eponymous movie has AI datacentres in her sights - just as Big Tech spending on memory chips sends PC and mobile prices spiralling up
-

Navigating culture to govern AI successfully
Data governance is critical for scaling AI safely, but the biggest hurdles are people, not technology. Here’s why moving governance out of IT and securing executive buy-in are key for AI success
Videos
-
Diversity in tech 2023: Bev White, Nash Squared
-
Suki Fuller, most influential woman in UK tech 2023, winner’s speech
-
Diversity in tech 2022: Explaining employee resource groups
-
Diversity in tech 2022: Mehdi Mobayen-Rahni, Tyl by NatWest
-
Diversity in tech 2022: Kerensa Jennings, BT
-
Diversity in tech 2022: Joel Gujral, Myndup
Search thousands of tech definitions
- What is a SAN? Ultimate storage area network guide
- What is HR technology (human resources tech)?
- What is DevOps? Meaning, methodology and guide
- What is compensation management?