IT for small and medium-sized enterprises (SME)
-
News
03 Jun 2026

SIT Committee urges Palantir exit in push to end US cloud grip
A Science, Innovation and Technology Committee report contains recommendations that would radically alter UK public sector IT, procurement and relationship with hyperscalers if adopted Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
News
02 Jun 2026

Data dive: Mapping the UK public sector’s hyperscale dependence
UK government and local authorities have built critical infrastructure amid a web of US hyperscaler cloud and other providers, which brings risks of exposure to a narrow set of non-UK suppliers Continue Reading
-
Feature
02 Jun 2026

The great datacentre backlash: The campaigners
In part one of a series looking at attitudes to datacentres, we look at the organisations that oppose new builds, concerns and motivations, what the industry thinks and what solutions might resolve the various impasses Continue Reading
By- Andrew Donoghue
-
Opinion
28 May 2026

The AI knowledge gap and how to close it
Equinix found big gaps in people’s knowledge about AI and how it is used in everyday life. MD James Tyler says we need to close that gap to nurture AI skills and to support AI projects Continue Reading
By- James Tyler, MD, Equinix UK
-
Opinion
28 May 2026

Realities of the AI age force sustainability to the fore
New standards force carbon accounting to be location-free. Meanwhile, AI and its energy appetite mean we have to build sustainability into an organisation's competitive edge Continue Reading
By- Shane Herath, Eco-Friendly Web Alliance
-
Feature
28 May 2026

CISO burnout: How to prevent contagion across the team
If employers fail to nip the problem of their CISO’s chronic, unmanaged stress in the bud, there could be serious consequences, not just for cyber security leaders themselves but for their teams too Continue Reading
By -
News
27 May 2026
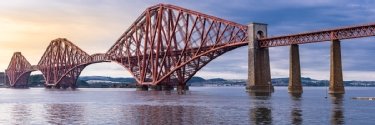
Scottish social enterprise supports national cyber efforts
Cyber and Fraud Centre has supported community cyber resilience in Scotland to the tune of £3m in its first year operating as a social enterprise Continue Reading
By- Alex Scroxton, Security Editor
-
News
27 May 2026

Datacentre dive: AI factory power draw changes the grid calculus
We look at energy as the key driver – and bottleneck – in development, and why water use is less of an issue now datacentres use liquid cooling over air cooling Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
News
27 May 2026

Datacentre dive: Do AI datacentre physics make on-premise unviable?
Does substantial GPU power draw and liquid cooling mean the end of the on-premise datacentre? We look at the AI factory revolution and find that a hybrid path for enterprises will likely still exist Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
News
27 May 2026

Datacentre dive: From rust belt to megawatt AI factory
We visited Terawulf’s Lake Ontario 750MW datacentre development. Photos and recordings weren't allowed, so we took notes and wrote them up in more traditional ways Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
News
27 May 2026

UKtech50 2026: Vote for the most influential person in UK technology
Our judges have selected the top 50 leaders from a long list of top-class nominees – now it’s your chance to tell us who you think is the most influential person in UK technology Continue Reading
By -
News
26 May 2026

UKtech50 2026: The longlist of the UK’s influential tech leaders
Each year, Computer Weekly launches a search for the most influential people in UK IT, asking the tech community who it thinks should be in the top 50 – here is the longlist of everyone nominated for 2026 Continue Reading
By -
News
14 May 2026

Bradford datacentre with heat reuse gains planning consent
Deep Green’s 5.6MW AI datacentre will take 24 months to build and will link up to an energy centre to heat buildings across Bradford city centre via pre-laid pipes Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
Opinion
13 May 2026

Can data sovereignty become a liability in war?
The recent Middle East conflict shows the contradictions inherent in modern data systems and the need to focus less on who controls data and more on how to protect the infrastructure Continue Reading
By- Moinul Zaber, research fellow, Institute of Development Studies
-
News
13 May 2026

Data dive: Power grid data shows birth of AI in UK datacentres
Electricity supply utilisation ratios show datacentre developer ‘land grab’, capacity switch-ons, the coming of Hopper and Blackwell GPUs, and usage ramping during training runs Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
News
11 May 2026

UK government renews calls to sign Cyber Resilience Pledge
Westminster renews calls for business leaders to sign up to its yet-to-be-launched Cyber Resilience Pledge, and highlights growth, and challenges, for the UK’s cyber economy Continue Reading
By- Alex Scroxton, Security Editor
-
News
08 May 2026

Node4: AI and agentic the future, but culture the key to unlock it
UK mid-market supplier showcases the three stages of AI – assistance, co-work and orchestration – but faces a reality in which most users have yet to arrive at first base Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
News
06 May 2026

Cloud and data sovereignty caught in a paradox
We asked the hyperscalers how they would respond to US court-ordered eavesdropping on foreign citizen data – and got responses that highlight a paradoxical situation Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
Feature
06 May 2026

Is cloud data sovereignty all just a case of ‘Trust me, bro’?
Hyperscaler cloud is inherently global. Does that make data sovereignty unattainable – especially given the powers US courts hold? We grilled the hyperscalers in an attempt to find out Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
News
05 May 2026

Google AI workers vote to unionise over IDF and US military tech
Unions send letter to management requesting recognition for Google DeepMind employees, in particular over the company’s involvement in hi-tech systems used in Gaza and Iran wars Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
News
30 Apr 2026

Almost half of UK businesses hit by cyber attacks
The government’s annual cyber security report reveals UK businesses are still struggling with the impact of attacks and breaches Continue Reading
By- Alex Scroxton, Security Editor
-
News
30 Apr 2026

Cloud revenues up 35% YoY in a hot market that’s accelerating
Synergy Research figures put Q1 cloud revenues at $129bn. Meanwhile, AWS, Microsoft and Google have 63% of the world market, which shows an acceleration delta of 13% Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
News
30 Apr 2026

Umbrella companies not working for IT contractors, survey finds
IT skills market impacted as contractors forced to use umbrellas or opt out altogether, while tax compliance remains deeply uncertain, with late payments and payslip inaccuracy rife Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
News
28 Apr 2026

Vect ransomware actually destructive wiper malware
Analysis of a form of ransomware called Vect has uncovered a serious flaw that breaks its core functionality and turns it from a locker to a wiper Continue Reading
By- Alex Scroxton, Security Editor
-
News
26 Apr 2026

UKtech50 2026 – help us find the most influential people in UK IT
Computer Weekly’s annual search for the 50 most influential people in UK technology is on – let us know who you would like to nominate for this year's list Continue Reading
By -
Feature
23 Apr 2026

AI drives software productivity – and challenges – for Motorway
We talk to Ryan Cormack of used car marketplace Motorway about how AI-driven development increases the speed and productivity of engineering and the challenges it brings Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
News
23 Apr 2026

AI adoption is rapid but many stuck at basic levels, says AWS
The UK could unlock £35bn of productivity – equivalent to the economy of Manchester – if organisations can move from basic use of AI to productive, often agentic, modes of working Continue Reading
By- Antony Adshead, Datacentre and cloud editor (acting)
-
News
17 Apr 2026

Surging CVE disclosures force NIST to shake up workflows
NIST announces big changes to the way it categorises and manages CVEs, which are set to have a big impact on how organisations manage patching and remediation Continue Reading
By- Alex Scroxton, Security Editor
-
News
16 Apr 2026

CyberUK 2026: UK lagging on legal protections for cyber pros
Ahead of next week’s CyberUK conference, the CyberUp Campaign for reform of the UK’s hacking laws urges the government to keep focus and proposes a four-pillar framework that would protect cyber professionals from prosecution Continue Reading
By- Alex Scroxton, Security Editor
-
News
15 Apr 2026

UK businesses must face up to AI threat, says government
Technology secretary Liz Kendall urges Britain’s business community to sit up and pay attention to emerging AI threats, following the debut of Anthropic’s new frontier model, Mythos Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
15 Apr 2026

Drone strikes show why key military principles apply to cloud data
One key thing every soldier knows is that bunching up under fire is a very bad idea. Here, a retired French general says CIOs need to apply the same principle to data in the cloud Continue Reading
By- Major General Laurent Boïté (retired)
-
News
14 Apr 2026

April Patch Tuesday brings zero-days in Defender, SharePoint Server
Microsoft’s latest Patch Tuesday update may be one of the largest in history, with more than 160 issues in scope Continue Reading
By- Alex Scroxton, Security Editor
-
News
07 Apr 2026

Russian cyber spies targeting consumer, Soho routers
The UK’s NCSC and Microsoft have shared details of an ongoing cyber espionage campaign targeting vulnerable network routers, orchestrated by Russian state actor Fancy Bear Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
02 Apr 2026

Identity and AI: Questions of data security, trust and control
The Computer Weekly Security Think Tank considers the intersection of AI and IAM. In this article, learn how AI-driven IAM projects must account for important questions around data protection, user trust, accountability and control. Continue Reading
By- Ellie Hurst, Advent IM
-
Opinion
01 Apr 2026

AI-driven identity must exist in a robust compliance framework
The Computer Weekly Security Think Tank considers the intersection of AI and IAM. In this article, learn how while AI‑driven identity solutions offer genuine value, they must be implemented within a robust framework of governance, privacy protection, and ethical responsibility. Continue Reading
-
Opinion
31 Mar 2026

Banning routers won’t fix what’s already broken
America's foreign-made router ban sparked valid debate about supply chains, geopolitics and trust, but the truth is that the ban addresses tomorrow’s procurement decisions far more than today’s security exposure. Continue Reading
By- Rik Ferguson, Forescout
-
Opinion
25 Mar 2026

Platformisation or platform theatre? Navigating cyber consolidation
The Security Think Tank looks at platformisation, considering questions such as how CISOs can distinguish between a truly integrated platform and 'integration theater, and how to protect unified platforms. Continue Reading
By- John Bruce, Quorum Cyber
-
News
25 Mar 2026

Emergency Microsoft, Oracle patches point to wider cyber issues
Emergency out-of-band patches from Microsoft and Oracle signal underlying security issues around update cycles and patching, and identity security and zero-trust, says the community Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
24 Mar 2026

Cyber platformisation is a skills issue for security teams
The Security Think Tank looks at platformisation, considering questions such as how CISOs can distinguish between a truly integrated platform and 'integration theater, and how to protect unified platforms. Continue Reading
By- Haris Pylarinos, Hack the Box
-
Opinion
23 Mar 2026

Cyber platformisation: Don't fall into the 'integration debt' trap
The Security Think Tank looks at platformisation, considering questions such as how CISOs can distinguish between a truly integrated platform and 'integration theater, and how to protect unified platforms. Continue Reading
By- Rik Ferguson, Forescout
-
News
20 Mar 2026

Scotland launches five-year AI strategy
Scottish deputy first minister says the country aims to become a leader in AI through responsibly harnessing the economic and social benefits of the technology Continue Reading
By -
News
19 Mar 2026

Cisa tells US organisations to harden endpoint management after Stryker attack
Last week’s cyber attack on the systems of a US medical services company by Iranian hacktivists has prompted an alert from Cisa, urging organisations to reinforce their defensive posture Continue Reading
By- Alex Scroxton, Security Editor
-
News
19 Mar 2026

Apple issues first Background patch for WebKit browser flaw
Apple’s first ever Background Security Update fixes a WebKit browser engine bug that could enable threat actors to see and steal important data from their victims Continue Reading
By- Alex Scroxton, Security Editor
-
News
17 Mar 2026

Digital IDs edge closer to practical reality for UK businesses
Industries and policymakers are strongly aligned on the need for digital company IDs for UK businesses, as progress is made towards the implementation of a practical standard Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
17 Mar 2026

Beyond integration theatre: Building stronger cyber platforms
The Security Think Tank looks at platformisation, considering questions such as how CISOs can distinguish between a truly integrated platform and 'integration theater, and how to protect unified platforms. Continue Reading
By- Joe Mayhew and Ahmed Tikail, PA Consulting
-
News
16 Mar 2026

Companies House restarts online services following cyber breach
Companies House was forced to pull its WebFiling service offline at the weekend after it emerged that a flawed update was putting data at risk of exposure Continue Reading
By- Alex Scroxton, Security Editor
-
News
16 Mar 2026

Cyber flywheel aims to kick-start UK cyber security startups
Company founder rallies CISOs, venture capital funders and government leaders to back startups in cyber security Continue Reading
By- Bill Goodwin, Computer Weekly
-
Opinion
13 Mar 2026

How CISOs can build a truly unified and resilient security platform
The Security Think Tank looks at platformisation, considering questions such as how CISOs can distinguish between a truly integrated platform and 'integration theater, and how to protect unified platforms. Continue Reading
By- Vaibhav Dutta, Tata Communications
-
Feature
12 Mar 2026

Vulnerability reports: Increase in quantity, decrease in quality?
Bug bounties have become a staple of the cyber security toolkit, offering researchers a way to get paid to find and report bugs and giving businesses a route to fix unknown flaws. However, this model is now facing scrutiny. What is driving these concerns? Continue Reading
By -
News
11 Mar 2026

UK government announces package to get more women in tech
The UK government aims to add billions of pounds to the economy through getting more women into the tech sector Continue Reading
By- Karl Flinders, Chief reporter and senior editor EMEA
-
News
11 Mar 2026

Mastercard bots target C-suite roles
Card giant offers SMEs a virtual chief financial officer through artificial intelligence technology, with other C-suite roles to follow Continue Reading
By- Karl Flinders, Chief reporter and senior editor EMEA
-
News
11 Mar 2026

Cyber industry welcomes women, but challenges persist
Three-quarters of women working in security say they feel comfortable in the field, but women are still much more likely to be laid off and face persistent challenges around career advancement, according to a report Continue Reading
By- Alex Scroxton, Security Editor
-
News
11 Mar 2026

Salesforce tracks possible ShinyHunters campaign targeting its users
Salesforce warns users of an uptick in malicious activity targeting Experience Cloud customers with misconfigured user settings via an open source tool Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
11 Mar 2026

Confidence in AI-powered cyber must be earned, not assumed
In security, familiar testing and validation approaches are not enough when it comes to AI. The question is not just whether an AI-powered tool works but how it actually behaves when it is stressed, manipulated, or forced to operate outside already known conditions. Continue Reading
By- Haris Pylarinos, Hack The Box
-
News
10 Mar 2026

Microsoft patches zero-days in .NET and SQL Server
Zero-days in .NET and SQL Server, and a handful of critical RCE bugs, form the nucleus of Microsoft’s March Patch Tuesday update Continue Reading
By- Alex Scroxton, Security Editor
-
News
09 Mar 2026

UK to launch cyber fraud squad in April
The UK’s Online Crime Centre, launching next month, will bring together government, police, intelligence agencies, banks, mobile networks and tech firms to take coordinated action against cyber fraud Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
06 Mar 2026

Platformisation without illusion: Separating integration from theatre
The Security Think Tank looks at platformisation, considering questions such as how CISOs can distinguish between a truly integrated platform and 'integration theater, and how to protect unified platforms. Continue Reading
By- Aditya K Sood, Aryaka
-
News
06 Mar 2026

Nordics ally with Baltics to accelerate digital wallet roll-out
Baltic and Nordic countries work together on a common certification system to support digital wallet applications Continue Reading
By- Gerard O'Dwyer
-
News
05 Mar 2026

Spyware suppliers exploit more zero-days than nation states
Exploitation of zero-days by commercial surveillance and spyware developers outpaced exploitation by nation-state actors last year, according to a report Continue Reading
By- Alex Scroxton, Security Editor
-
News
04 Mar 2026

Iranian hacktivists muster their forces but state APTs lay low
Hacktivist activity surrounding the Iran war is sky-high but Iran’s state-backed cyber espionage actors have yet to show their hands, giving security teams a valuable window of time to shore up their defences Continue Reading
By- Alex Scroxton, Security Editor
-
News
04 Mar 2026

Zero-day in Android phone chips under active attack
Google and Qualcomm have tag-teamed a serious vulnerability in the chipsets used in Android mobile devices, which has been exploited in the wild as a zero-day Continue Reading
By- Alex Scroxton, Security Editor
-
News
04 Mar 2026

Tycoon2FA phishing platform dismantled in major operation
A Europol-led sting against the infamous Tycoon2FA MFA bypass phishing service has been successful, with operations disrupted and ringleaders and cyber criminal users identified Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
03 Mar 2026

Open cyber standards key to cross-platform integration
The Security Think Tank looks at platformisation considering questions such as how CISOs can distinguish between a truly integrated platform and 'integration theater, and how to protect unified platforms. Continue Reading
By- Stephen McDermid, Okta
-
Opinion
03 Mar 2026

NS&I’s modernisation programme: A £3bn lesson in how to lose public trust
The UK Public Accounts Committee’s description of NS&I’s digital modernisation as a ‘full-spectrum disaster’ should concern far more than technology teams Continue Reading
By- Ben Terrett
-
News
26 Feb 2026

Qilin crew continues to dominate ransomware ecosystem
The Qilin ransomware gang remained ‘top dog’ in January 2026, with over 100 observed cyber attacks to its name, amid a rapidly evolving and fragmenting cyber criminal ecosystem Continue Reading
By- Alex Scroxton, Security Editor
-
News
25 Feb 2026

Application exploitation back in vogue, says IBM cyber unit
IBM’s X-Force unit observes an uptick in the exploitation of vulnerable public-facing software applications Continue Reading
By- Alex Scroxton, Security Editor
-
News
23 Feb 2026

€126bn in Dutch tech projects blocked by permits and grid limits
Ex-ASML chief Peter Wennink’s deregulation solution triggers warnings from academics and government advisors Continue Reading
By- Kim Loohuis
-
News
19 Feb 2026

Minister wants ‘logical conclusion’ to review of digital evidence in light of Post Office scandal
House of Lords debate saw government minister make an ambiguous promise in regard to the treatment of computer evidence in court Continue Reading
By- Karl Flinders, Chief reporter and senior editor EMEA
-
News
18 Feb 2026

Flaws in Google and Microsoft products added to Cisa catalogue
Cisa has added six CVEs to its Kev catalogue this week, including newly disclosed issues in Google Chromium and Dell RecoverPoint for Virtual Machines, and some older flaws as well Continue Reading
By- Alex Scroxton, Security Editor
-
News
18 Feb 2026

0APT ransomware crew makes embarrassing splash
A ransomware gang called 0APT has attracted attention, but many of its victims may not even be real, and its operators are being accused of over-egging their criminal pudding Continue Reading
By- Alex Scroxton, Security Editor
-
News
17 Feb 2026

Businesses may be caught by government proposals to restrict VPN use
Labour proposals to restrict social media use to people aged 16 and under could have unintended consequences for businesses using virtual private networks Continue Reading
By- Bill Goodwin, Investigations Editor
-
Feature
17 Feb 2026

The evolution of threat research: Looking beyond best-of-breed
Traditional models of threat research as a service are changing and evolving towards a more bespoke model that puts more control in the hands of end-user cyber teams Continue Reading
-
News
11 Feb 2026

CVE volumes may plausibly reach 100,000 this year
The number of vulnerabilities to be disclosed in 2026 is almost certain to exceed last year's total, and may be heading towards 100,000, according to analysis Continue Reading
By- Alex Scroxton, Security Editor
-
News
10 Feb 2026

February Patch Tuesday: Microsoft drops six zero-days
Microsoft releases patches for six zero-day flaws in its latest monthly update, many of them related to security feature bypass issues Continue Reading
By- Alex Scroxton, Security Editor
-
News
10 Feb 2026

Researchers delve inside new SolarWinds RCE attack chain
Researchers at Huntress and Microsoft have shared findings from their analysis of a new SolarWinds Web Help Desk vulnerability Continue Reading
By- Alex Scroxton, Security Editor
-
News
10 Feb 2026
Is the EU’s free trade deal with India the dawn of a new era?
Trade deal between European Union and India simplifies the visa system for professionals from India, which could make the country’s suppliers more accessible Continue Reading
By- Karl Flinders, Chief reporter and senior editor EMEA
-
News
04 Feb 2026

SolarWinds RCE bug makes Cisa list as exploitation spreads
Exploitation of CVE-2025-40551, an RCE flaw affecting SolarWinds Web Help Desk, appears to be spreading, with defenders on high alert Continue Reading
By- Alex Scroxton, Security Editor
-
News
03 Feb 2026

Ransomware gangs focus on winning hearts and minds
Ransomware-as-a-service operations are increasingly seeking to forge connections with employees, contractors and trusted partners of their target organisations as an alternative to straight-up hacking, says NCC Continue Reading
By- Alex Scroxton, Security Editor
-
News
03 Feb 2026

Kendall names Barnsley as UK’s first tech town
The UK government has named Barnsley as the nation’s first ‘tech town’, with initiatives to boost education, health and local businesses Continue Reading
By- Brian McKenna, Enterprise Applications Editor
-
News
29 Jan 2026

Security now one of the UK’s fastest-growing career paths
The number of people working in the cyber security field has almost trebled in the 2020s, with one cyber professional for every 68 businesses in the UK Continue Reading
By- Alex Scroxton, Security Editor
-
News
27 Jan 2026

Wave of ShinyHunters vishing attacks spreading fast
The ShinyHunters hacking collective that caused chaos in 2025 is ramping up a new voice phishing campaign, with several potential victims already identified Continue Reading
By- Alex Scroxton, Security Editor
-
News
27 Jan 2026

Broken decryptor leaves Sicarii ransomware victims adrift
A coding error in an emergent strain of ransomware leaves victims unable to recover their data, even if they cooperate with the hackers’ demands Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
26 Jan 2026

AI claims are cheap: The challenge is to work out what's real
The Security Think Tank considers what CISOs and buyers need to know to cut through the noise around AI and figure out which AI cyber use cases are worth a look, and which are just hype. Continue Reading
By- Ellie Hurst, Advent IM
-
News
21 Jan 2026

AI slop pushes data governance towards zero-trust models
Organisations are implementing zero-trust models for data governance thanks to the proliferation of poor quality AI-generated data, often known as AI slop Continue Reading
By- Alex Scroxton, Security Editor
-
Feature
16 Jan 2026

Dutch researcher’s AI breakthrough tackles the structured data paradox
Table representation learning unlocks 99% of organisational data that remains unused Continue Reading
By- Kim Loohuis
-
News
15 Jan 2026

Cyber body ISC2 signs on as UK software security ambassador
Professional cyber association ISC2 pledges support to UK government’s Software Security Ambassador scheme, part of the recently unveiled Cyber Action Plan Continue Reading
By- Alex Scroxton, Security Editor
-
News
14 Jan 2026

Microsoft DCU uses UK courts to hunt down cyber criminals
Microsoft has taken down the RedDVS cyber crime-as-a-service network after obtaining a UK court order, marking its first civil legal action outside of the US Continue Reading
By- Alex Scroxton, Security Editor
-
News
13 Jan 2026

Microsoft patches 112 CVEs on first Patch Tuesday of 2026
January brings a larger-than-of-late Patch Tuesday update out of Redmond, but an uptick in disclosures is often expected at this time of year Continue Reading
By- Alex Scroxton, Security Editor
-
News
13 Jan 2026

‘Dual-channel’ attacks are the new face of BEC in 2026
Business email compromise remains a significant threat as cyber fraudsters deploy a more diverse range of tactics against their potential victims, according to a report Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
13 Jan 2026

Cutting through the noise: SaaS accelerators vs. enterprise AI
The Security Think Tank considers what CISOs and buyers need to know to cut through the noise around AI and figure out which AI cyber use cases are worth a look, and which are just hype. Continue Reading
By- Richard Watson-Bruhn, PA Consulting
-
Opinion
09 Jan 2026

From promise to proof: making AI security adoption tangible
The Security Think Tank considers what CISOs and buyers need to know to cut through the noise around AI and figure out which AI cyber use cases are worth a look, and which are just hype. Continue Reading
By- Aditya K Sood, Aryaka
-
News
08 Jan 2026

Like it or not, AI will transform cyber strategy in 2026
Bubble or no bubble, from cyber skills to defensive strategies to governance, risk and compliance, artificial intelligence will remake the cyber world in 2026 Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
08 Jan 2026

Security Think Tank: Stop buying AI, start buying outcomes
The Security Think Tank considers what CISOs and buyers need to know to cut through the noise around artificial intelligence and figure out which AI cyber use cases are worth a look, and which are just hype Continue Reading
By- Rik Ferguson, Forescout
-
News
06 Jan 2026

Fujitsu UK job cuts as staff pay the price for failures of top executives
Troubled IT giant’s staff are paying the price for senior management failures over Post Office scandal Continue Reading
By- Karl Flinders, Chief reporter and senior editor EMEA
-
News
30 Dec 2025

Oldest victim of Post Office scandal awarded OBE in New Year Honours 2026
The New Year Honours List 2026 conferred an OBE on the oldest living victim of the Post Office scandal, as well as hailing members of the UK technology community Continue Reading
By- Brian McKenna, Enterprise Applications Editor
-
News
30 Dec 2025

Top 10 technology ethics stories of 2025
Here are Computer Weekly’s top 10 tech ethics stories of 2025 Continue Reading
By- Sebastian Klovig Skelton, Data & ethics editor
-
News
29 Dec 2025

Top 10 cyber security stories of 2025
AI dominated all tech conversations this year, but the concerns of cyber security professionals extend far beyond. From remote work to supply chains, quantum to identity, there were plenty of other topics for the industry to chew over in 2025. Continue Reading
By- Alex Scroxton, Security Editor
-
News
18 Dec 2025

Fortinet vulnerabilities prompt pre-holiday warnings
Analysts track exploitation of two vulnerabilities disclosed last week by Fortinet Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
18 Dec 2025

Passwords to prompts: Identity and AI redefined cyber in 2025
As we prepare to close out 2025, the Computer Weekly Security Think Tank panel looks back at the past year, and ahead to 2026. Continue Reading
By- Daniel Gordon, PA Consulting
-
Opinion
18 Dec 2025

Cyber resilience will define winners and losers in 2026
As we prepare to close out 2025, the Computer Weekly Security Think Tank panel looks back at the past year, and ahead to 2026. Continue Reading
By- Nick New, Optalysys
-
News
17 Dec 2025

ClickFix attacks that bypass cyber controls on the rise
NCC’s monthly threat report details the growing prevalence of ClickFix attacks in the wild Continue Reading
By- Alex Scroxton, Security Editor
-
Opinion
17 Dec 2025

Security platform consolidation in 2026: The AI imperative
As we prepare to close out 2025, the Computer Weekly Security Think Tank panel looks back at the past year, and ahead to 2026. Continue Reading
By- John Bruce, Quorum Cyber


