The real story behind The Imitation Game film
Turing also made a breakthrough against a German enciphering machine more sophisticated than Enigma, named ‘Tunny’ by the British. The algorithms used to make inroads on Tunny were incorporated into the making of Tommy Flowers’ Colossus computer. Winston Churchill ordered the ten ‘Colossi’ to be destroyed at the end of the war.
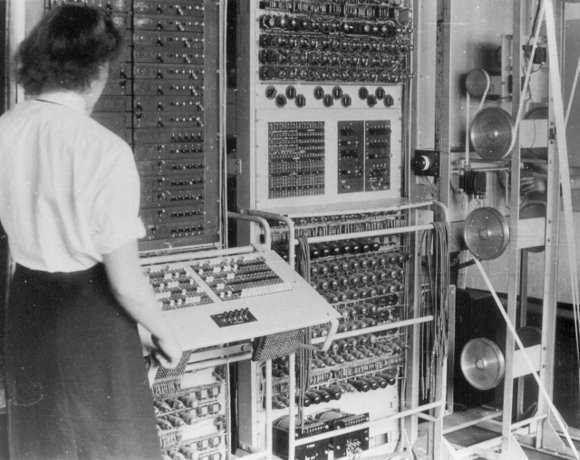
Colossus was the world’s first programmable electronic computer and aided in deciphering the encrypted messages sent between Hitler and his generals during World War II. The power of Colossus significantly reduced the time it took to decipher codes, accelerating the Allies’ code-breaking operation. The National Museum of Computing (TNMOC) states that over the course of the war, 10 Colossus computers, worked by 550 people, had managed to break 63 million characters of high-grade German communications.
The information taken from these decrypted messages is believed to have shortened the war by many months, according to TNMOC. However, according to Professor Sir Harry Hinsley, official historian of British Intelligence in World War II, it may have shortened the war by up to two years.
In 1992, computer engineer and programmer Tony Sale began to reconstruct a Colossus computer. With the help of his team, Sale succeeded in 2007. On completion of the rebuild, the Colossus cracked the Lorenz code used by the German armed forces in 3.5 hours. This compares with modern-day computer software, which broke the code in 46 seconds. The rebuild of the Colossus is on display in a public gallery at TNMOC at Bletchley Park.