
Blue Planet Studio - stock.adobe
Dutch accuse UK of ‘damaging confidence’ by disclosing details of EncroChat police collaboration
The Dutch Public Prosecution Service claims Britain has damaged confidence by disclosing details of an international investigation into the EncroChat encrypted phone network to the courts
Prosecutors in Rotterdam have accused the UK of “damaging confidence” of European law enforcement bodies by disclosing details of a joint police operation to infiltrate the EncroChat encrypted phone network.
The Dutch Public Prosecution Service (OM) has written to prosecutors in the Netherlands claiming that the UK wrongly disclosed documents from confidential meetings between law enforcement and prosecutors to the British courts.
The letter dated 24 March 2021 appears designed to counter suggestions made in UK court hearings that the Dutch had a role alongside the French Gendarmerie in harvesting millions of supposedly secure messages from EncroChat phones.
An international police operation based on data collected from the cryptophone network has led to hundreds of arrests in the UK and other countries, including France, Holland, Germany and Sweden.
Brits accused of breaking confidentiality
The letter claims that British prosecutors disclosed confidential details of the international police operation against EncroChat as they sought a ruling on the admissibility of intercepted EncroChat messages in UK courts.
Law enforcement agencies from France, Holland, the UK and other countries, held a series of meetings at European institutions – identified as Europol and the European Union agency for criminal justice cooperation, Eurojust – to coordinate action against EncroChat.
“The purpose of these meetings was to discuss with various representatives from different countries whether [they] see opportunities to cooperate and, if so, what legal and practical way this should be done,” the letter said.
Unlike the UK, France and the Netherlands are permitted to “tap streaming data” and use it in evidence, according to the letter.
That discrepancy between UK law and laws in France and the Netherlands led to court hearings last year to decide whether the EncroChat material could be used to bring prosecutions against British criminal suspects.
“Witnesses were heard and documents submitted to substantiate the position that data are admissible as evidence,” the letter said.
The British “released documents from confidential meetings” and disclosed information that the joint French and Dutch investigation team had communicated to the authorities “through diplomatic channels”, according to the letter.
“Such information should not have been released in this way,” it stated.
Dutch deny involvement in EncroChat hacking
The Public Prosecution Service acknowledges that the Dutch, through operation “26Lemont”, and the French, through operation “Emma”, worked closely on the EncroChat investigation.
According to a press release issued by Europol in July 2020, France and the Netherlands have cooperated on investigations into the use of encrypted communications services by criminal groups since 2018.
The Forensic Laboratory of the French Gendarmerie (IRGN) and the National Forensics Institute (NFI) in Holland went on to work on a two-year project with University College, Dublin, to study how to break passwords of encrypted systems in February 2019.
The £2.3m project, Cerberus, has developed advanced methods and techniques to crack encrypted information used by criminals, by using the processing power of computer graphics cards and exploiting vulnerabilities to bypass encryption.
The project played a key role in helping French cyber experts “read messages on the EncroChat server”, the NFI announced yesterday.
“Criminals thought they were safe from the police and the judiciary and discussed their cases carefree. It turned out to be a wealth of information. The Dutch investigation services also benefited.”
Investigators for the French Gendarmerie’s digital crime unit, C3N, in Pontoise on the outskirts of Paris, were able to trace the servers used by the EncroChat phone network to a datacentre run by OVH in Roubaix.
Computer Weekly has established that the French made copies of the servers and shared them with the Dutch in January 2019, October 2019, February 2020 and June 2020, as part of the initial investigation into EncroChat.
By March 2020, the French had set up a national investigation unit at C3N employing 60 gendarmes working in data analytics, technical and judicial investigating, and on 27 March 2020, a Rotterdam court authorised Dutch police to collect data from EncroChat phones.
The French internal security agency, DGSI, supplied a “software implant” which harvested data stored on infected phones and transmitted it to a server operated by the French Gendarmarie.
French investigators began collecting EncroChat live data from phones on 1 April 2020, making it available to Dutch police through a secure computer link.
The French and Dutch formalised their relationship on 10 April 2020, when they formed a joint investigation team (JIT) into EncroChat, with support from Europol and Eurojust.
According to the Dutch National Forensics Institute, the French Gendarmarie has built a hardware platform at Pointoise, drawing from the experience of the Dutch and French collaborators, to assist European investigating authorities to automatically decrypt passwords used to scramble information.
UK accused of disclosing details of hacking operation
The UK’s National Crime Agency (NCA) had been collaborating with the Gendarmerie on EncroChat since early 2019, and the Gendarmerie disclosed to the NCA that it had developed a way to penetrate EncroChat in January 2020.
According to a Court of Appeal judgment dated 5 February 2021, the UK’s NCA applied for a targeted equipment interference (TEI) warrant to legally access EncroChat messages from the joint investigation team.
The warrant was initially approved by Kenneth Parker, a judicial commissioner, on 5 March 2020 on behalf of the Investigatory Powers Commissioner’s Office (IPCO), the independent surveillance regulator.
It was updated to widen the scope of data collection from EncroChat phones on 26 March 2020, when it was approved by the investigatory powers commissioner, Brian Leveson.
The warrant appeared to suggest that the interception had been jointly undertaken by the French Gendarmarie and Dutch law enforcement working together.
“The conduct below is being undertaken by the French Gendarmerie and Dutch law enforcement working together in a joint investigative team,” it said, before giving details of the interception operation.
Under the proposed plan, an implant created by the JIT would be deployed from an update server in France to EncroChat phones worldwide.
The implant would collect data already stored on phone handsets, including chat messages, images, notes, usernames, each phone’s unique International Mobile Equipment Identity (IMEI), passwords, stored chat messages, images, notes and geolocation data.
During the second stage of the operation, the implant would gather messages as they were sent, which meant the JIT was often able to read messages long before they had been seen by the intended recipient.
The implant would also instruct EncroChat handsets to provide a list of Wi-Fi access points near the device, potentially supplying the JIT with the name and identification number of the Wi-Fi point, which could help to locate and identify suspects.
Europol, with the assistance of police officers from the NCA, Holland and France, planned to use automatic algorithms to triage the data to identify threats to life.
The NCA received the data the next day and conducted its own triaging exercise to identify high-risk crimes including firearms and terrorism, and material relating to ongoing investigations.
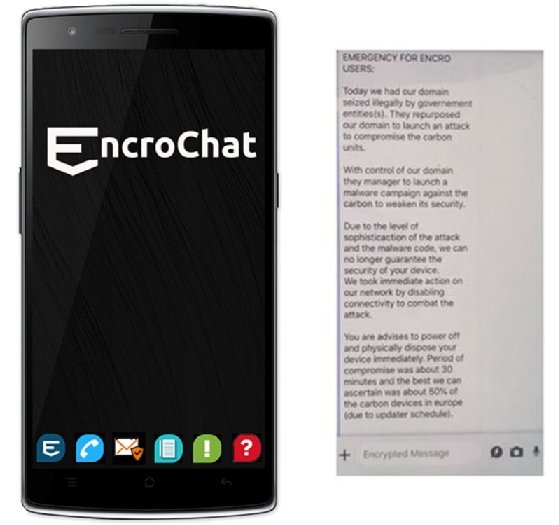
The harvesting continued until 14 June 2020, two days after people with EncroChat phones received an anonymous message warning them that the network had been compromised and advising them to dispose of their handsets immediately.
Dutch had no role in designing intercept
The OM is adamant, however, in its letter to Dutch prosecutors, that it had no involvement with the design of the intercept.
“The French authorities have made it known that the interception tool was developed by them,” it stated, adding that the French had declared the interception technology as “a military state secret”.
“That fact also seems to be insufficiently appreciated and respected by the British authorities,” the prosecution service wrote.
The letter also denies that the Dutch shared details of the criminal investigation with the French investigators to bolster their case for applying for judicial authority to carry out the hack.
The OM told the Dutch courts that the French Gendarmerie carried out the attack, and that the French had already collected information from the phones before the French and Dutch formed the joint investigation team.
“The Netherlands did not request France prior to the JIT or during the JIT to apply [for] authority whereby ‘live’ information was obtained from the exchanged chat between users of this communication service,” according to one Dutch court document.
The issue is sensitive in the Netherlands, said Wim van de Pol, a Dutch crime journalist who has reported extensively on EncroChat.
Because the Dutch Public Prosecution Service told the Dutch courts that it had no involvement in the interception operation, the Dutch courts have been able to assume, on the basis of European trust, that the fundamental rights of suspects have not been violated, he said.

This has been called into question by documents from the UK National Crime Agency, first reported on crimesite.nl, which suggest the operation was carried out jointly by the French and the Dutch.
“If that is true, in court cases there will be questions about what they stressed – that it was a French hack, with no involvement of Dutch police. If proven otherwise, they didn’t report truthfully,” said Van de Pol.
A judgment by the UK Court of Appeal on 5 February 2021 found that messages were extracted from EncroChat phones while they were in storage in the phones’ memory, rather than when they were being transmitted.
The decision sidestepped UK laws, which have prevented material obtained from live intercepts from being used as evidence in criminal cases, by defining the messages harvested from EncroChat as the product of equipment interference, rather than interception.
The NCA, working in collaboration with regional organised crime units and other forces, has made more than 1,550 arrests under Operation Venetic, the UK’s response to the takedown of EncroChat.
The operation has also resulted in the seizure of five tonnes of class A drugs, 155 firearms and £57m in cash.
Read more on Information technology (IT) in Germany
-
![]()
Dutch Supreme Court approves use of EncroChat evidence
-
![]()
Germany: European Court of Justice hears arguments on lawfulness of EncroChat cryptophone evidence
-
![]()
Three years on, EncroChat cryptophone hack nets 6,500 arrests and seizures of €900m
-
![]()
Cyber crime officer says French legal challenges to EncroChat are ‘hype’







