
Europol
‘They protect the law while breaking it’: Inside Europol’s shadow IT system
Under pressure to deliver in the fight against serious cross-border crime, Europol built and operated a shadow data analysis platform containing large volumes of sensitive information, which operated without key legal and technical safeguards
By Apostolis Fotiadis | Gaicomo Zandonini | Luděk Stavinoha | Frida Thurm | Lydia Emmanouilidou | Bill Goodwin | Sebastian Klovig Skelton
Europol, the European Union’s (EU) police agency, operated a shadow data repository containing vast amounts of sensitive personal information and used it for years beyond its lawful scope, according to internal documents and whistleblower accounts.
Described by former officials as a “shadow IT environment”, the system lacked basic security or data protection safeguards required under EU law. It was used to store and analyse highly sensitive data – phone records, identity documents and geolocation information – including details of people who were not suspected of a crime.
This investigation by Solomon, Correctiv and Computer Weekly, based on leaked emails, internal reports and testimonies from former officials, found that in practice, the system became the agency’s primary environment for large-scale data analysis, despite lacking essential controls over who could access or modify the data.
For the first time in the agency’s history, several former high-ranking officials have come forward to reveal that the use of this shadow environment to store vast amounts of data – and the use of a clandestine intelligence tool known internally as the “Pressure Cooker” – had been concealed from the EU’s top privacy watchdog until 2019.
“They protect the law while breaking it,” one former senior official said of Europol.
The findings come at a pivotal moment: the European Commission is expected to propose new legislation that would expand Europol’s mandate and double its annual budget. At the same time, Europol’s executive director, Catherine De Bolle, stepped down on 1 May, after leading the agency for eight years.
Conservative MP David Davis, an outspoken critic of creeping data collection by governments, said that the findings, “if true, point to serious failures of oversight, legality and data protection”. He added: “Systems appear to have operated significantly beyond what is lawful and processed vast quantities of sensitive information, including information about innocent individuals, without proper scrutiny.”
Responding to this investigation, a Europol spokesperson said the agency had reported its operational data processing systems and applications to the EU’s privacy watchdog in a transparent manner: “The allegation that Europol ‘kept hidden’ information about systems or processing environments is a misrepresentation of the facts.”
A shadow IT environment
At the centre of the agency’s shadowy data practices was a system known as the Computer Forensic Network (CFN), an environment holding vast amounts of sensitive personal information.
According to Europol, the system was established in 2012 to process complex operational data linked to investigations it supported. Its purpose was to provide a “secure, compartmentalised” environment for processing information that could not be handled in its existing systems, due to its volume, format, or potential security risks, including malware from digital devices.
By 2019, the CFN held at least two petabytes (PB) of data – almost 420 times bigger than Europol’s primary database for non-forensic work – and effectively held almost all of Europol’s operational data.
Under EU law, sensitive personal data – whether provided by member states, collected during cross-border investigations, or transferred by online platforms such as Facebook or Telegram – is subject to strict rules governing how it can be stored, accessed and analysed. But internal documents and witness accounts indicate that, in this case, effective safeguards were absent.
Previously unseen evidence indicates that vast volumes of sensitive data were made available to Europol’s analysts via the CFN, a system with significant security and privacy flaws that did not fully log who accessed data, or whether it had been modified or deleted. For years, it operated without effective official scrutiny, even as it became central to the agency’s analytical work.
The agency is designed to function as a central, artificial intelligence (AI)-powered hub, analysing large volumes of personal and criminal data in near real time to identify patterns and leads. Based in the Hague, Europol’s more than 1,000 staff sit at the centre of European policing. The agency pools and analyses data from national law enforcement authorities across the EU, supporting investigations into terrorism, child sexual abuse, serious organised crime and cyber crime.
To understand how Europol’s shadow IT system took shape, it is necessary to go back to a moment of crisis.
Pressure to deliver
In November 2015, coordinated attacks across Paris killed 130 people and injured hundreds more. Amid reports of police failures, pressure on Europol intensified. “We were really expected to step up at that point,” Europol’s then-director, Rob Wainwright, recalled last year. “That was the moment where we had to deliver.”
Europol set up Task Force Fraternité, and member states’ law enforcement authorities began sending large volumes of data to the agency: phone records, intelligence reports and travel information. Much of it ended up in the CFN system. Among the data ingested, for example, were phone logs of individuals who happened to be in the vicinity of the Bataclan attacks.
The expectation was clear: Europol would turn this flood of information into actionable intelligence to help trace and prevent new terrorist plots.
The role of the “shadow IT system” expanded dramatically after the attacks.
Europol told this investigation that its policy stated that Europol’s Cyber Crime Centre (EC3) – a unit created within the Operations Directorate in 2013 – and its ICT Operations Unit co-managed the CFN. That policy was still in force in 2019 and “known to all relevant stakeholders”.
But according to five former Europol officials who spoke on the condition of anonymity, the agency’s EC3 effectively seized control of the CFN during the tenure of then-executive director Wainwright.
The network that became a ‘black hole’
The CFN, established in 2012, formed part of Europol’s Forensic IT Environment (FITE). It had originally been designed to store and initially process, or filter, the growing amounts of digital material and link it to specific investigations, under strict handling and data protection rules.
Within a few years, though, the CFN evolved far beyond its original purpose, becoming what one former senior official described as a “black hole” for unregulated data analysis by Europol’s cyber crime unit. Large volumes of data could be stored and analysed with fewer constraints than in the agency’s formal systems.
Wainwright, who led the agency at the time, responded to this investigation that his recollection “is not great on specific issues and details that date back to a period of 8-14 years”.
He added that he does recall “working very closely” with Europol’s data protection officer, Daniel Drewer, “and the relevant data supervisory authorities on the establishment and promotion of a strong data protection framework”, and that this “was an essential part of Europol’s mission and a core strategic priority”.
The threat of a ‘complete shutdown’
When new data protection laws came into effect across Europe in May 2018, protecting data became a legal imperative. By the following year, the scale of Europol’s non-compliant data practices had become impossible to ignore.
On 15 February 2019, a five-page report by Drewer – who continues to serve as the agency’s internal data protection officer – landed on the desks of Europol’s three deputy executives.
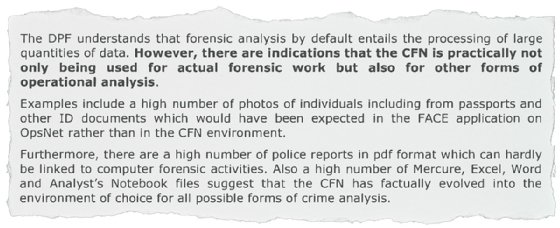
The message was blunt: 99% of Europol’s data was being stored and processed in the CFN, without basic data protection and security safeguards.
In effect, a system designed to pre-process raw bulk data had become the agency’s primary platform for large-scale crime analysis. Europol investigators were able to sift through vast troves of personal data, including information they were not legally entitled to retain, and repurpose it for criminal investigations.
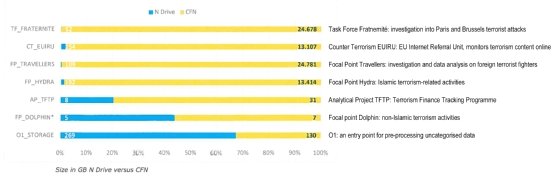
“There are indications that the CFN is practically not only being used for actual forensic work but also for other forms of operational analysis,” Drewer wrote. The volume and diversity of files in the database, he said, suggested that “CFN has factually evolved into the environment of choice for all possible forms of crime analysis”.
Drewer had time to review only a selection of Europol’s investigations, known as analytical projects. He found, just for the limited selection of analytical projects he reviewed, that the CFN held nearly 25 million records – more than 20 times the 1.2 million records held in Europol’s primary system for non-forensic work.
Drewer warned that data protection safeguards used elsewhere in Europol had not yet been fully implemented on the CFN. And many users appeared to have administrator rights, suggesting that some operations might have been launched without a data protection impact assessment (DPIA) or, in the case of sensitive data, seeking prior approval from the EU’s data watchdog.
Except for the use of the CFN for Taskforce Fraternité – an exceptional case for which mitigating measures had been put in place – Europol’s data protection function had not been consulted about the use of the CFN for non-forensic tasks, he said.
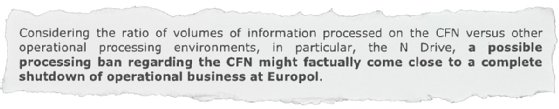
Unless Europol overhauled the entire system, Drewer warned of “a possible processing ban” by the European Data Protection Supervisor (EDPS), the EU’s independent privacy watchdog. Such a ban could “factually come close to a complete shutdown of operational business at Europol”, while severely damaging trust with member states, Drewer wrote.
Parallel processing environments
The enormous scale of irregular practices at the heart of Europe’s main criminal database, unveiled by Drewer’s report, has remained unknown to the public, as well as lawmakers, until today.
Former Europol officials interviewed by this investigation described how personnel within the Operations Directorate – which is responsible for criminal investigations – worked to install additional computing and storage capacity to the system outside of regular procedures. New tools and applications for data processing were developed within this environment, without external oversight.
“Having a parallel processing environment where guardrails cease to exist is cheaper, faster and more effective,” a former senior Europol official told this investigation. “But without these, anyone is at the mercy of the guy in front of the screen,” he said. In other words, decisions about who could access Europol’s data were left to Europol staff, with little oversight.
Europol maintains that the CFN was part of a “regulated processing environment” that included a research and development environment, and said the former official’s comments were “a misrepresentation of the facts”.
Grasping the scale of the problem
On 1 April 2019, Europol’s then-executive director, Catherine De Bolle, formally notified the EU’s data protection watchdog, the EDPS, of Drewer’s findings, after intense internal deliberations over how to respond.
The disclosure triggered what became known as the “Big Data Challenge” – a years-long standoff between Europol and the external watchdog, culminating in an order from the EDPS that Europol delete data it kept in breach of EU law.
Publicly, the dispute came to focus on data retention. But previously unpublished internal documents reviewed by this investigation suggest the concerns ran deeper. They point to security vulnerabilities embedded in the system itself.
Inside the agency, staff were working to grasp the scale of the problem.
A comprehensive security assessment, triggered by Drewer’s findings and conducted in early 2019, found that CFN lacked “baseline security controls applicable to an operational environment”. Addressing the issues, the report noted, would require Europol to abandon the system “as it stands today and implement a new setup” – from scratch.
Dozens of grave security vulnerabilities within the CFN system, listed in reports obtained via Freedom of Information (FoI) requests, reveal a pattern of systemic failures:
- “ineffective assignment of security roles and responsibilities”
- “insufficient management of privileged access rights”
- “unrestricted software installation”
- “incompliance with the Europol security rules”
- “lack of password management”
- “lack of administrative usage logs”, “insufficient protection of log information”, “insufficient event logging and monitoring”
- “insufficient network access control”

Taken together, these failures meant that access to sensitive data could not be reliably tracked, controlled, audited or safeguarded. Access controls and audit logs are not mere technical formalities, experts say, but fundamental security and accountability safeguards, required under EU law.
“The alleged existence of large numbers of administrator accounts is very concerning and an obvious breach of the integrity and confidentiality requirements,” said Peter Sommer, an independent digital forensics expert. He explained that administrators can access, modify, or delete any data – including system logs – making it difficult to trace activity and increasing the risk of abuse and external attacks.
“Unnecessary multiplication of administrator facilities makes it easy for rogue employees to cause harm, but also is a strongly favoured gateway for external hackers,” said Sommer.
Steven Murdoch, professor of security engineering and head of the Information Security Research Group at University College London, told Computer Weekly that the agency’s failure to implement system controls could result in breaches of confidentiality or allow undetected data tampering. “Another consequence is that, if breaches are detected, it might be impossible to identify who is responsible,” he said.
Failure to track data access could also raise questions about the reliability of evidence used in criminal prosecutions. “Data related to criminal investigations can be extremely sensitive, and breaches of confidentiality could compromise ongoing investigations or sources of intelligence. If information was modified without authorisation, its value as evidence in courts could be invalidated,” said Murdoch.
Responding to questions about the management of CFN users, a Europol spokesperson said that a Forensic IT Environment (FITE) use and management policy had been in place since 2012, and was still in force and known to all stakeholders in 2019.
They said the policy “contained dedicated user access and audit logging provisions” for the CFN.
Data held on Europol’s forensic network at risk from security failures
Steven Murdoch, professor of security engineering and head of the Information Security Research Group at University College London, reviewed the findings of Europol’s 2019 internal security assessment for Computer Weekly, which flagged up 32 issues, including nine high-severity issues in the Computer Forensic Network (CFN).
“Based on the information available, I would agree with the ratings. While it’s rare for systems to have perfect security, the more sensitive information they hold, the higher the expectation of security. For something as important as the CFN, I would expect few, if any, high-severity issues,” he said.
Murdoch said he was particularly concerned that there were inadequate controls to prevent software from being installed on such a high-security network, leaving it at risk of both malware and inadvertent data breaches.
Peter Sommer, an independent digital forensics expert, said the alleged presence of many people with administrator rights on Europol’s CFN could expose the agency to security risks from rogue employees and hackers.
Administrators have unlimited powers to access, modify and delete every item of information and every programme in a computer system. They also have the power to modify or delete log files, which record who accessed what data.
“Unnecessary multiplication of administrator facilities makes it easy for rogue employees to cause harm, but also is a strongly favoured gateway for external hackers,” he said.
Three information security experts from the Open Rights Group (ORG), a digital rights campaign group, also reviewed the findings of Europol’s 2019 internal security assessment for Computer Weekly.
Jim Killock, the ORG’s executive director, said the experts’ analysis found that Europol’s CFN had serious and widespread cyber security issues relating to access control, asset management, network security and other issues.
He said that having many users with admin rights to the CFN posed a security risk that was compounded by other failures, such as a lack of administrative logs, which could allow for human error or a malicious actor to modify forensic data.
“In a worst-case scenario, these findings might indicate that there are insufficient safeguards to prevent unauthorised personnel from accessing and modifying data,” he said.
By the time the scale of the problem was clear, the system had already become deeply embedded in Europol’s operations.
Although Europol initiated a project to deliver an alternative data analysis platform with the controversial US tech company Palantir, the project collapsed in 2017.
Abandoning the platform was therefore no longer a realistic option.
Instead, Europol sought to bring it into compliance – a process that would take years of negotiation with the EDPS.
In a written response, Europol said it had disclosed the system in 2019 to the European Data Protection Regulator “in the interest of full transparency”, describing it as a necessary environment for processing complex operational data, particularly large or technically challenging datasets. The agency said reforms had been underway since 2019 to replace the CFN with a new forensic environment and align practices with data protection requirements.
The EDPS continued to monitor the system in the years that followed – but key problems persisted.
As of late 2023, the watchdog found that it was still not always possible to determine whether specific personal data had been accessed or modified. An EDPS spokesperson told this investigation that limitations in the logging system meant that investigators could only “infer” that data had been “accessed” or “modified”.
In February 2026, the EDPS informed the Joint Parliamentary Scrutiny Group – an oversight committee of European and national parliamentarians – that it would close its monitoring of the CFN after nearly a decade of exchanges with Europol, even though 15 out of 150 recommendations had not been implemented.
Those outstanding issues, the watchdog noted, concerned “issues of particular importance”, including core security safeguards.
‘Pressure Cooker’ shielded from scrutiny
Even as Europol’s leadership rotated and worked with the EDPS to address problems in its data systems, elements of the infrastructure appear to have remained outside formal oversight.
The existence of one of the hidden systems, known internally as the “Pressure Cooker”, emerges through leaked internal emails and whistleblower accounts from former Europol officials. References to the system appear as early as 2019, right before Europol formally disclosed compliance issues to the EDPS.
An internal email reveals that Europol’s online counter-terrorism unit, the Internet Referral Unit (IRU), had set up a pilot area to gather open data from the internet, without the support of Europol’s ICT operations.
The IRU referred to the system as the Internet Facing Operational Environment (IFOE). But the IRU’s project was effectively a shadow IT operation that existed outside of the official project of the same name.
When the head of the Internet Referral Unit demanded urgent ICT support for IRU’s IFOE, it was flatly turned down.
“What you call ‘IFOE’ is an environment prepared in emergency mode under the ‘Pressure Cooker agreement’, and is in its entirety managed by IRU,” he was told.
There was no relationship between the IFOE project that the ICT had in its work programme and the IRU’s “unofficial” version.
“There is clearly a severe misunderstanding between what ICT calls IFOE (future state, designed and agreed by all stakeholders) and what you call IFOE,” the email added.
On 5 October 2022, a Europol staff member sent an email marked “Importance: High” to senior officials, warning that regulators might soon become aware of the “irregular situation” with the Pressure Cooker and the Internet Facing Operational Environment, which Europol used to collect data for investigations from open sources on the internet.
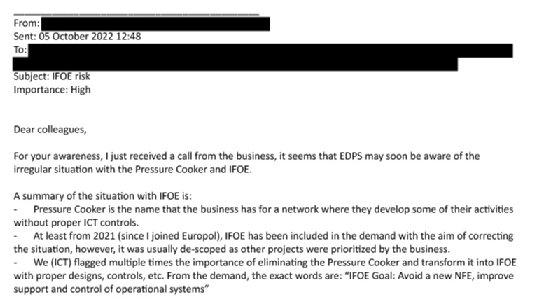
“We (ICT) flagged multiple times the importance of eliminating the Pressure Cooker and transforming it into [a system] with proper designs, controls, etc,” the staffer wrote. “However, it was usually de-scoped as other projects were prioritized by the business.”
According to former insiders, the system was understood within parts of the agency as a space where operational data could be stored and analysed quickly without the constraints of EU law.
Oversight, however, depended largely on what information Europol chose to disclose.
“You have to understand,” a former top Europol official told this investigation, “when we say inspection in this case, we don’t mean a raid with IT experts monitoring systems and confiscating servers. We are talking about a polite conversation.”
And shadow IT systems that were not clearly identified or formally presented might not be examined, raising questions about whether shadow IT systems might still be in use today.
EDPS told this investigation that it was not made aware of the Pressure Cooker during its Big Data Challenge inquiry, which started in April 2019.
The former official said it was “quite possible” that even as Europol worked with regulators to address problems in the CFN, “people within the operations devised clusters where they could keep doing data analysis without any of the newest checks and balances”.
Europol seeks to regularise its systems
The EDPS said that it became aware of the term “Pressure Cooker” when it appeared in Europol’s ICT work plan for 2022, where it was used as a shorthand for a proposed interim internet-facing environment.
Fast forward to 2024, and Europol had plans in place to build a new system to respond to situations that required rapid analysis of data gathered from the internet.
Known as the Internet Facing Operational Environment – Quick Response Area, the system was intended to be legally compliant and address previous internal concerns raised over the lack of adequate controls around the “Pressure Cooker”.
However, as late as February 2026, the EDPS warned that the IFOE-QRA “risks becoming a full-fledged parallel environment to Europol’s regular operational environment”. That created a risk that Europol would fall foul of regulations that only allowed personal data to be processed for limited purposes.
EPDS also said it sees a risk of Europol staff going on “fishing expeditions” that infringe upon fundamental rights, by collecting personal data without relevance to any ongoing criminal investigations.
In response to this investigation, Europol claims that the “Pressure Cooker” is simply the internal name for its Internet Facing Operational Environment and that it operates in accordance with the law.
It said the suggestion that Europol was seeking to collect information without relevance to criminal investigations outside the scope of the Europol Regulation, the legal framework which governs its operation, was a “misrepresentation” of the facts.
An expanding mandate
Europol is entering a new phase of expansion.
The European Commission is expected to propose new legislation that would expand the agency’s mandate and significantly increase its capacity to collect and process data, as part of a broader effort to turn Europol into a “truly operational police agency”.
In March, the European commissioner for migration and home affairs, Magnus Brunner, proposed to double Europol’s staff and budget, in front of the European Parliament’s LIBE Committee, which oversees the agency’s work.
The push comes even as Europol faces questions about its data practices.
British MP David Davis said the issues identified by this investigation raise questions for the British government, where data supplied by Europol had been used by UK police forces.
“We must have clarity from the Home Office as to whether UK data or prosecutions are affected and demand full transparency. We must also be told whether any personal data of entirely innocent British citizens is being stored in Europol’s systems and, if so, why it is being stored and why the UK government is allowing it to be stored,” he added.
“The integrity of our justice system depends on evidence being gathered, handled and governed lawfully at every stage,” he said.
Computer Weekly contacted the UK’s National Crime Agency (NCA), which acts as a liaison between UK law enforcement bodies and Europol, about the findings of this investigation – including whether it was aware of the parallel processing within the shadow IT estate and if it will now review the data sharing mechanisms and practices in place with Europol as a result – but received no response by time of publication.
Jim Killock, executive director of Open Rights Group, a digital campaign group, said the revelations of this investigation call for “urgent scrutiny”.
“Europol requires the highest levels of data security and integrity, as an investigating organisation, holding data on individuals who may be accused or prosecuted, or are witnesses to very serious crimes. Europol’s decisions need to be trusted and able to withstand intense legal scrutiny,” he said.
“As a matter of urgency, Europol needs to explain how deep these problems go, and whether they extend to questions over evidential integrity.”
Catherine De Bolle, Europol’s executive director at the time of this investigation, declined to be interviewed for this story.
Europol response
Responding to detailed questions from this investigation, Europol said its IT estate was “a regulated data processing environment”.
Europol said it kept the European Data Protection Supervisor (EDPS) regularly updated about issues with the system, and has been committed to transparency and scrutiny of the Computer Forensic Network (CFN).
It added that, after the topic of CFN was brought to the attention of the EDPS in April 2019, Europol’s executive director and the data protection officer had a “very constructive” meeting with then-EDPS chief Giovanni Butarelli.
“Afterwards, the EDPS was regularly informed by Europol on the progress made and the activities of the task force,” said a spokesperson. “Accordingly, Europol provided the EDPS in a proactive manner information about the required improvements of the CFN back in 2019, hence Europol addressed its identified improvement needs in full transparency towards its data protection supervisor, which were addressed accordingly through the referred internal Europol task force.”
Europol said that the term “Pressure Cooker” referred to Europol’s Internet Facing Operational Environment (IFOE), and that the agency has reported to the EDPS about its operational data processing systems and applications in a transparent manner.
“The allegation that Europol ‘kept hidden’ information about processing environments or systems is a misrepresentation of the facts,” it said.
On the “inherent risks identified” with the IFOE Quick Response Area by the EDPS, Europol added that this is a “normal” part of the prior consultation process, and that it works to implement all relevant actions to reduce the associated data protection risks to an acceptable level.
“In the FITE [Forensic IT Environment], data from publicly available sources, such as in relation to terrorist content online, is collected and triaged, before being entered into Europol’s operational data environment,” said a spokesperson. “The allegation of Europol seeking to collect information without relevance to criminal investigations outside the scope of its tasks under the Europol Regulation is a misrepresentation of the facts.”
Additional research by Anna Mahtani.





