
clrcrmck
Retailer FatFace pays $2m ransom to Conti cyber criminals
Retailer FatFace paid out a $2m ransom to restore its data following a January 2021 cyber attack by the Conti ransomware syndicate
Fashion retailer FatFace has paid a $2m ransom to the Conti ransomware gang following a successful cyber attack on its systems that took place in January 2021, Computer Weekly has learned.
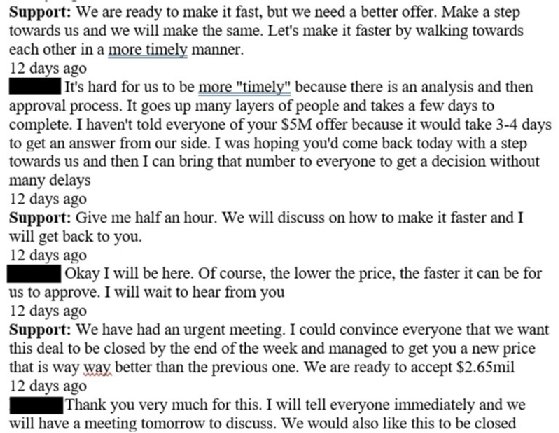
The ransomware operators had initially demanded a ransom of $8m, approximately 213 bitcoin at the prevailing rate, but were successfully talked down during a protracted negotiation process, details of which were shared with Computer Weekly after being uncovered by our sister title LeMagIT.
During discussions, the negotiator for the Covid-hit retailer told Conti’s representative that since shutting its bricks-and-mortar stores, it was making only 25% of its usual revenues from its e-commerce operation, so to pay an $8m ransom would mean the end of the business. This was rejected by Conti on the basis that FatFace’s cyber insurance policy, held with specialist Beazley Furlonge, covers extortion to the tune of £7.5m – substantially more than $8m.
Ultimately, a significant factor in the reduction was the apparent deletion from FatFace’s storage area network (SAN) of a number of virtual machines (VMs) and data from primary business apps, including its electronic point of sale (Epos) system, SAP Business Intelligence reporting, merchandising application, warehouse management systems, SQL server cluster and Citrix Hosts, the recovery of which would cause further damage. Conti’s representative denied responsibility for this, and it is unclear from the negotiation logs how it happened.
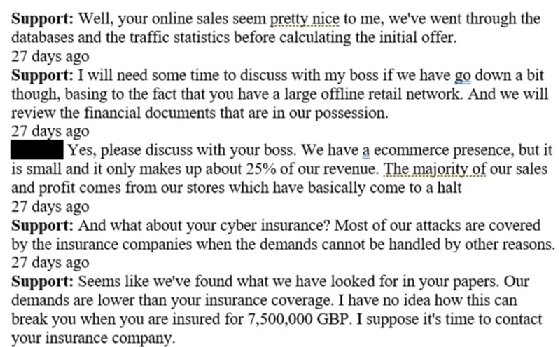
Conti/FatFace negotiation logs
The Conti gang told FatFace’s negotiators that its red team – note the use of standard legitimate research terminology – entered the firm’s network via a phishing attack on 10 January. From there, the team was able to obtain general administrative rights and began to move laterally through the network, identifying the retailer’s cyber security installations, Veeam backup servers and Nimble storage. The ransomware attack itself was executed on 17 January and saw more than 200GB of data exfiltrated.
As it closed out the negotiation, the Conti gang advised FatFace’s IT teams to implement email filtering, conduct employee phishing tests and penetration testing, review their Active Directory password policy, invest in better endpoint detection and response (EDR) technology – the gang apparently recommends Cylance or VMware Carbon Black for this – better protect the internal network and isolate critical systems, and implement offline storage and tape-based backup.
A spokesperson for the retailer said: “FatFace was unfortunately subject to a ransomware attack which caused significant damage to our infrastructure.
“Thanks to a monumental effort from the FatFace team, alongside external security and legal experts, FatFace was able to quickly contain the incident, restore business operations and then undertake the process of reviewing and categorising the data involved – a significant task which has taken considerable time.
“We have notified and are working with the Information Commissioner’s Office, police authorities (via Action Fraud) and the National Cyber Security Centre in respect of the incident,” said the spokesperson
“Our teams have worked tirelessly to minimise disruption to our highly valued customers and fellow employees, and we would like to thank them for their support during this challenging period. We have taken various steps to protect our systems from any future reoccurrence.
“Details of the attack and steps taken are part of a criminal investigation so at this stage we are unable to comment any further. We recognise that ransomware attacks are an issue which more and more organisations are having to grapple with in the current threat landscape,” they added.
Breach disclosure
In an email shared by a recipient with reporters, initially Information Security Media Group which was first to report the breach, FatFace told customers it had determined that some customer information, including names, postal and email addresses, and limited credit card data, had been compromised in the attack. It is offering affected customers a 12-month subscription to Experian’s identity theft service.
“Customers who had personal information, including partial payment card data (which cannot be used to purchase anything fraudulently on the card, so customers are not required to cancel any cards), involved have been notified as appropriate. They will have received an email from us, marked private and confidential due to the nature of the communication, which is intended for the individual concerned. Customers who have not received an email are not required to take any specific steps in response to the incident at this time,” said the FatFace spokesperson.
“The responsibility we have to our customers and colleagues is our highest priority and we continue to invest in security measures to mitigate the growing range of risks faced by businesses. We are now operating as usual and FatFace remains a safe place to shop online, or in-store when shops reopen,” the firm added.
An ICO spokesperson confirmed a live investigation into the incident. “Fatface has made us aware of an incident and we are making enquiries,” it said. “People have the right to expect that organisations will handle their personal information securely and responsibly.
“When a data incident happens, we would expect an organisation to consider whether it is appropriate to contact those affected, and to consider whether there are steps that can be taken to protect them from any potential adverse effects,” said the ICO.
Conti: an evasive Ryuk descendant
A successor to the Ryuk ransomware, Conti is a live, global threat that has hit multiple organisations in recent months, mostly in Western Europe and North America, with at least 10 known victims in the UK that have had their data published on the gang’s leak site.
The majority of known victims are in the retail, manufacturing and construction sectors, according to Sophos researchers.
The ransomware most commonly arrives through disclosed software or hardware vulnerabilities, remote desktop protocol (RDP) exploitation, or phishing, as was the case with FatFace. It is known to be highly evasive, deploying complex custom tooling and novel tactics, techniques and procedures (TTPs) to obfuscate it, and make it harder, though not impossible, for research teams to obtain samples for study.
According to Coveware, Conti’s operators tend to carefully research their targets and scale their ransom demands accordingly – however, the average ransom payment made as of February 2021 is a little over $740,000. Recovery times are generally slightly less than with other ransomware, and victims who have paid currently have a 100% success record in decrypting their data. The decryptor tool is, reportedly, straightforward and easy to use.
As with much other ransomware, the operators of Conti act in some ways as though they are running a professional, legitimate security testing service. This can be seen clearly in the chat logs, which in parts read like a standard technical support log, and in which Conti’s representative at one point reassures FatFace’s negotiator that there is nothing to be gained from forcing the retailer into bankruptcy, and that the gang values its reputation.
Read more about ransomware
- The average amount paid out by ransomware victims has grown almost threefold to more than $300,000 per incident, according to a report.
- Record-breaking double-extortion cyber attack sees REvil gang exfiltrate financial data from Taiwan-based PC manufacturer Acer.
- Ransomware gangs targeting vulnerable instances of Microsoft Exchange Server, making patching an even greater priority.








