
Christian Horz - stock.adobe.com
NCSC warns high-risk individuals of Signal and WhatsApp social engineering attacks
NCSC advises on countermeasures for high-risk individuals over phishing attacks on encrypted messaging services, such as Signal, WhatsApp and Facebook Messenger
High-risk individuals have been urged to take steps to reduce their exposure to social engineering attacks against encrypted messaging apps, including Signal, WhatsApp and Facebook Messenger.
The UK’s National Cyber Security Centre, part of GCHQ, warned that politicians, academics, journalists and lawyers are at greater risk from social engineering attacks by nation state-backed hackers attempting to gain access to messaging services.
Government officials have also been targeted by China, the Russian Federal Security Service (FSB) – which hacked the encrypted emails of a former head of MI6 – and Iran’s Islamic Revolutionary Guard Corps (IRGC).
The NCSC’s alert follows warnings from Google’s Threat Intelligence Group in February that Russian state-backed groups were making increasing efforts to target the Signal accounts of people of interest to the Russian intelligence services.
Hacking groups were using social engineering techniques to trick high-risk individuals into linking their Signal, or other messaging accounts to devices controlled by the hackers, allowing them to read messages sent and received by the target.
Techniques include attempts to trick victims into sharing login or account recovery codes, to persuade people to join group chats, to impersonate someone known to the victim, or to send malicious links or QR codes.
Journalists targeted
Journalists working on sensitive stories using the Signal messaging services were targeted with phishing messages in late January.
Stefania Maurizi, an Italian investigative journalist, told Computer Weekly that she had been working on investigations into the activities of US Immigration and Customs Enforcement (ICE), the Israel Defence Forces and Italian police when she received a phishing message purporting to be an update to Signal.
“Since I have worked on WikiLeaks for over a decade and on the Snowden files, I became acutely aware of how journalists are a target,” she said. Checks revealed there was no Signal update available for her phone.
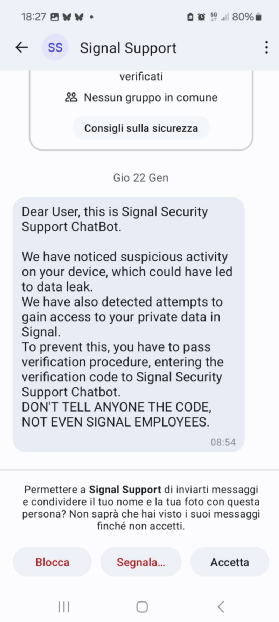
Maurizi was sent a second phishing message a few days later on a second phone purporting to come from the “Signal security support chatbot”, a non-existent service.
Russian attackers have exploited Signal’s “linked devices” feature that enables Signal to be used on multiple devices simultaneously by sending the victim malicious QR codes masquerading as legitimate Signal messages.
If the attacks are successful, future messages will be sent simultaneously to the victim and to the hacker, allowing the hacker to eavesdrop on secure conversations without having to compromise the victim’s device.
The NCSC advises people at risk not to share sensitive information through messaging apps, which may be difficult for some users, to use two-step authentication in Signal, and passkeys.
It recommends regularly checking in settings for devices linked to a messaging account, reviewing membership of discussion groups and removing or verifying any unrecognised participants and the use of disappearing messages.
FSB hacked Brexit supporters
Computer Weekly revealed in 2022 that a Russian FSB-linked hacking group, known variously as Coldriver, Seaborgium, Callisto and Star Blizzard, hacked and leaked emails and documents belonging to a former head of MI6, and other members of a right-wing network campaigning for an extreme hard Brexit. The hacking group also conducted attacks against journalists, MPs and an NGO in the UK.
Academics from the universities of Bristol, Cambridge and Edinburgh, including the late Ross Anderson, professor of security engineering, first published researched in 2023 warning that linked desktop versions of Signal and WhatsApp could be compromised if accessed by a border guard or a malicious actor, enabling them to read all future messages.
Last year, Microsoft warned that a Russian-linked group dubbed Storm-2372 was targeting victims on WhatsApp, Signal and Microsoft Teams, building up a rapport before sending them invites to online events or meetings through phishing emails.
Read more about Phishing
- Tycoon2FA phishing platform dismantled in major operation: A Europol-led sting against the infamous Tycoon2FA MFA bypass phishing service has been successful, with operations disrupted and ringleaders and cyber criminal users identified.
- Phishing prevention: How to spot, stop and respond to scams: From email scams to BEC attacks, phishing is one of the biggest fish organisations must fry. Get advice on how to identify, prevent and respond to phishing schemes.








