
alexskopje - stock.adobe.com
FBI arrests distributors accused of selling An0m encrypted phones to crime groups
Working with overseas law enforcement, the FBI has arrested eight people and named a further 13 accused of distributing An0m phones to organised crime groups
The FBI, working with overseas law enforcement officers, has arrested eight people accused of supplying An0m encrypted phones to organised crime groups.
Their arrests follow joint police operations in 16 countries which resulted in more than 500 arrests of criminals involved in drug trafficking, money laundering and violent crime.
Criminal gangs were unaware that the An0m phone network was controlled by the FBI and that police were able to read encrypted messages for at least 18 months.
Six law enforcement officials have also been arrested for tipping off criminal groups about police investigations.
The US is seeking the prosecution of a further nine individuals who are accused of knowingly selling An0m encrypted phones to organised crime groups.
An indictment published yesterday names 17 people accused of running an operation to supply phones and provide technical support to criminal gangs.
They are accused of racketeering and conspiracy, multiple offences of trafficking controlled substances and money laundering.
The phones were used to distribute illegal drugs to Australia, Asia, Europe, the US and Canada, and to launder money.
An0m administrators, agents and distributors named
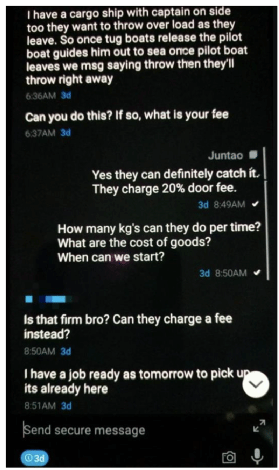
Administrators, agents and distributors named in the US legal document allegedly described the An0m phones to potential clients as “designed by criminals for criminals”.
The people named included Joseph Hakan Ayik, a Turkish citizen who is accused of influencing criminal associates to use encrypted phones. Australian law enforcement officials said he was given access to an An0m phone by undercover agents. He went on to recommend the phones to other associates, unaware that they were controlled by the FBI.
Australian Federal Police commissioner Reece Kershaw said Ayik was likely to be at risk from the criminals he supplied. “Given the threat he faces, he’s best-off handing himself in as soon as he can,” he said.
According to the indictment, Ayik, along with Dominico Catanzariti, an Australian citizen, and Maximilian Rivkin, a Swedish citizen, acted as administrators for the An0m network. They were able to initiate new subscriptions to An0m, remove accounts, and remotely wipe and reset devices to remove evidence of money laundering and drug crime.
The indictment names Erkan Yusef Dogan and Baris Tukel, Australians living in Turkey alongside Ayik and Rivkin, as “influencers” who encouraged the criminal underworld to use the encrypted devices. They have “built a reputation for their knowledge and expertise in the hardened encrypted device field and use that power, knowledge and expertise” to influence others.
The indictment lists Abdelhakim Aharchaou and Seyyed Hossein Hosseini, both Dutch citizens, Alexander Dmitrienko, a Finish citizen living in Spain and Shane Geoffrey May, an Australian living in Indonesia, as distributors of the phones.
Also named are Edwin Harmendra Kumar, an Australian, Omar Malik and Miwand Zakhimi, both citizens of the Netherlands, and Osemah Elhassen, an Australian living in Columbia.
According to the indictment, distributors and agents sold An0m devices and collected subscription fees based on a schedule for different geographic regions. The fee in Europe was around €1,000 to €1,500, in Australia it was A$1,700 and in Canada it was C$1,700 for a six-month subscription.
Phones sold for bitcoin
Payments were made in bitcoin and other cryptocurrencies to protect the users’ anonymity and were laundered through shell companies to hide the proceeds.
The individuals allegedly targeted people who were involved in international drug trafficking, money laundering and other crimes. They told customers that An0m was not subject to US law or the Patriot Act, to build up trust for An0m as a secure system for illegal activity.
The administrators, distributors and agents remained anonymous even from each other and their clients, communicating using a system of names and email handles. They suspended the service to phones and remotely deleted their contents if they suspected law enforcement or an informant was using the device as part of an investigation.
Criminals are accused of selling more than 12,000 An0m encrypted devices and services to at least 300 crime syndicates operating in over 100 countries. In one case, a criminal group sent pictures showing hundreds of kilograms of cocaine hidden in shipments of pineapples and bananas. Another image showed drugs hidden in cans of tuna.

The FBI, working with the Australian Federal Police, covertly harvested more than 27 million messages in near real time. The FBI had access to messages from the phones which were copied to a server based outside the US. The agency reviewed the messages for criminal activity and passed them on to other countries to investigate.
Phantom Secure takedown
This investigation began after Canada-based encrypted device company Phantom Secure was dismantled by the FBI in 2018, forcing many criminals to seek alternative devices.
An0m became more popular after police shut down the EncroChat encrypted phone network in 2020 and, in March 2021, a takedown operation into another encrypted phone network, Sky ECC, led to more criminals adopting An0m.
The An0m platform was also used by corrupt law enforcement officials to communicate with transnational criminal organisations. They used it to pass crime groups sensitive information and notify them of pending law enforcement action, said Suzanne Turner, an FBI agent responsible for the San Diego Field Office.
“These crimes resulted in the arrest of six law enforcement officers and dozens of cases opened during the course of the investigation,” she told a press conference.
Read more about encrypted phone networks
- Police in 16 countries carry out raids after Australian Police and the FBI crack an encrypted An0M communications network used by crime groups.
- More than 1,600 police and law enforcement officials conduct drug raids after the compromise of an encrypted mobile phone network that has parallels with EncroChat.
- US issues arrest warrants for the CEO of Sky Global and a former distributor for racketeering, aiding and abetting the distribution of illegal drugs by supplying encrypted phones to criminals.
Read more on Privacy and data protection
-
![]()
Europol provides detail on Ghost encrypted comms platform takedown
-
![]()
Police make arrests after hacking Ghost encrypted comms app
-
![]()
Canadian arrested by France after cooperating with US on Sky ECC cryptophone investigation
-
![]()
Encrypted mail service Tuta says it was wrongly accused of being a front for intelligence services








