
alexskopje - stock.adobe.com
French legal challenge over EncroChat cryptophone hack could hit UK prosecutions
Lawyers are challenging the legality of a French police operation to harvest tens of thousands of messages from the EncroChat encrypted phone network in a move that could overturn criminal prosecutions in the UK
French police unlawfully intercepted text messages from tens of thousands of encrypted phones in an operation that led to thousands of arrests across Europe, lawyers claim.
Investigators from France’s digital crime unit infiltrated the EncroChat encrypted phone network in April 2020, capturing 70 million messages.
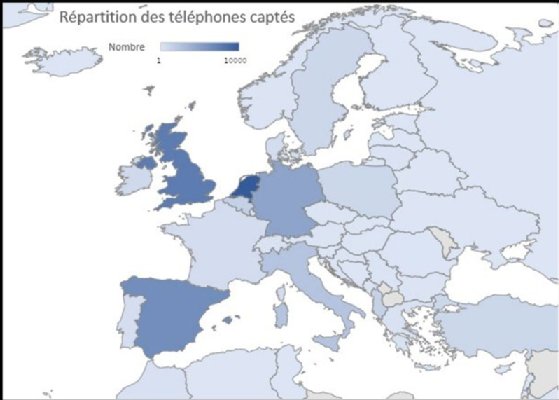
The operation, supported by Europol, led to arrests in the UK, Holland, Germany, Sweden, France and other countries of criminals involved in drug trafficking, money laundering and firearms offences.
Paris-based defence lawyers Robin Binsard and Guillaume Martine, founders of the French law firm Binsard Martine, have filed claims in French courts arguing that the interception is unlawful under the French Code of Criminal Procedure and other French laws (see box: Legal grounds against French EncroChat operation).
The lawyers say the investigators went beyond the legal authorisation given by a court in Lille by carrying out “massive data collection involving tens of thousands of mobile phones and tens of millions of messages”.
They are also questioning the lawfulness of the Gendarmerie’s refusal to disclose any details of the hacking operation – on the grounds of defence secrecy – under the French Constitution. And they are questioning the validity of orders made by the Lille court authorising the investigation.
If the challenge is successful, it is likely to raise questions about more than 250 prosecutions currently underway in the UK which make use of text messages, photographs and notes harvested from EncroChat phones by the French Gendarmerie.

Britain’s National Crime Agency (NCA), working with regional police forces, has made around 1,550 arrests in the UK, based on the EncroChat evidence supplied by French computer experts.
“If we have a decision saying the way the French collected the EncroChat messages was illegal, most other judges worldwide should reach the same conclusion. That evidence was collected by French authorities and under French law,” Binsard told Computer Weekly.
French investigators began intercepting unencrypted messages from EncroChat handsets on 1 April 2020, and by 27 April had amassed 68,750,000 messages from 32,477 phones in 121 countries, according to French legal documents.
Defence secrecy
Binsard and Martine are challenging the Gendarmerie’s refusal to reveal any details of how it carried out the interception of the EncroChat phones on the grounds of defence secrecy.
Forensic experts in the UK have argued that the Gendarmerie’s silence has led to an evidential “black hole” that has broken long-established principles which ensure that evidence is properly acquired and secured before being used in legal cases.

“We need [documents from the Gendarmerie] even if it is a defence secret. We have to have access to them. If we don’t, we cannot have a fair trial”
Robin Binsard, Binsard Martine
Under French law, the Gendarmerie is obliged to provide an explanatory note on the techniques used to obtain the intercept evidence and a certificate to authenticate the intercepted phone data and messages obtained from EncroChat phones.
“We need those documents even if it is a defence secret. We have to have access to them. If we don’t, we cannot have a fair trial,” said Binsard.
The French lawyers applied to the court of appeal in Nancy, in north-eastern France, in February, seeking further disclosure of evidence about how the hacking was carried out.
A judge has asked the Gendarmerie to provide further technical details of the hacking operation.
Hacked phones outside jurisdiction of French courts
The lawyers also argue that investigators at the French National Gendarmerie’s centre for the fight against digital crime, C3N, went beyond the legal authority granted by judges in a court in Lille.
The Lille court gave authorisation to the Gendarmerie to investigate the activity of EncroChat in France, which was accused of illegally importing encrypted devices into the country.
A judge authorised an investigation into the role of the company’s representative, identified as Eric Miguel, who leased servers for EncroChat through Virtue Imports, a company registered in Vancouver Canada, that were hosted by French software-as-a-service company OVH at its datacentre in Roubaix.
According to legal documents, only 380 of the 32,477 phones hacked by C3N were on French territory, putting nearly 98% of phones outside French legal jurisdiction.
The operation was “clearly a massive and indiscriminate capture of computer data unrelated to the alleged association of criminals led by Eric Miguel or even any criminal activity”, the lawyers said in a legal opinion.
“Almost all of the hacked phones, and therefore intercepted communications, thus do not, in reality, fall within the jurisdiction of the French judge,” it says.
Court order authorising data capture invalid
Binsard and Martine argue that a court order to divert EncroChat messages to a “capture device” controlled by the French Gendarmerie on the eve of the interception operation was also unlawful.
The order failed to specify a duration for the operation, required under article 706-102-3 of the French Code of Criminal Procedure, and should therefore be declared “null and void”.
Subsequent court orders extending the interception operation are also unlawful and should be voided by the court, they claim.
“We will ask them to destroy all of the messages,” said Binsard.
Court orders that prevented technology companies providing services for EncroChat from taking any action that could affect the operation of EncroChat’s infrastructure also face legal challenges.

They include an order to prevent domain name registrar Gandhi SAS and hosting company DNS Made Easy from taking any action that impacted the EncroChat.ch internet domain and related subdomains.
Another order required the cloud service provider OVH not to take any action that would impact the network infrastructure, virtual machines and IP addresses associated with EncroChat.
Although French law allows for the interception of data, it does not permit “blocking” or “modification” orders, according to the law firm.
EncroChat has become politicised
Binsard said EncroChat had become politicised and that it was not clear how the courts would react to legal challenges in France.
“All of the judges want to protect this investigation, so it is difficult to predict. According to the law, we should win, but the judge may try to protect the use of EncroChat traffic, even if they have to do so illegally,” he said.
Binsard said defence lawyers may refer the case to France’s constitutional council to decide whether the French Constitution has been breached, if they are not granted access to more details about how the French Gendarmerie carried out the hacking on EncroChat.
The case may ultimately go to the European Court of Human Rights as a potential breach of Article 8 of the European Convention on Human Rights, which protects the right to privacy.
The case of Big Brother Watch and Liberty v UK in 2018 found that the UK’s mass surveillance programmes did not “meet the quality of law” and were not capable of limiting “interference” to that “necessary in a democratic society”.
Legal grounds against French EncroChat operation
1. Failure to specify duration of interception authorised by a court order
A court order authorising investigators to re-route EncroChat traffic to a capture device run by the French Gendarmerie does not specify the duration of the measure. This is in breach of article 706-102-3 of the Code of Criminal Procedure.
Defence lawyers are calling for the order to be declared null and void.
2. Cancellation of further court orders
Defence lawyers argue that annulment of one court order for failing to specify a duration must lead to the cancellation of three subsequent court orders granting extensions to the intercept operation.
They are calling for the destruction of intercepted messages gathered during this period.
3. Network modifications were unlawful
Court orders taken out to prevent the two domain name service companies and French software-as-a-service company OVH from carrying out any operation that interfered with the Encrochat.ch domain names were unlawful.
Article 706-102-1 of the Code of Criminal Procedure allows law enforcement to intercept data but does not allow “blocking” orders against the domain name service providers. Other court orders that required “modification of network routing rules” also fell outside the Code of Criminal Procedure.
Defence lawyers argue that six court orders authorising the operation against EncroChat should be cancelled as they “very clearly” exceed the provisions of the Code of Criminal Procedure.
4. Interception should have been limited to phones in use on French territory
Defence lawyers argue that interception of messages on EncroChat phones should have been limited to phones in use on French territory.
They argue that the interception of EncroChat phones was “massive and indiscriminate” and went beyond the investigation authorised by the Lille court into the illegal import of encrypted EncroChat devices into France.
The capture method should be considered “illegal and void”.
5. Defence secrecy
The Gendarmerie has refused to disclose any technical details of the interception operation against EncroChat or to provide a certificate of authenticity of the seized data, required by French law.
Defence lawyers argue that the data capture was therefore illegal and should be declared void.
Read more on Smartphone technology
-
![]()
French supreme court dismisses legal challenge to EncroChat cryptophone evidence
-
![]()
German court unclear whether intercepted EncroChat cryptophone messages are legally admissible
-
![]()
Germany: European Court of Justice hears arguments on lawfulness of EncroChat cryptophone evidence
-
![]()
Three years on, EncroChat cryptophone hack nets 6,500 arrests and seizures of €900m








