Uncontrolled cyber attacks on UK cyber defenders’ radar
Uncontrolled cyber attacks are just as much a threat as targeted attacks, according to the UK’s cyber defence agency, which continues to consider a major cyber attack imminent
The UK’s National Cyber Security Centre (NCSC) considers preparing for uncontrolled cyber attacks just as important as preparing for targeted ones, as it continues to brace for an attack of national significance.
Fearing reckless attacks as much as controlled attacks was one of the biggest lessons of 2017, NCSC chief Ciaran Martin told The Guardian, citing WannaCry an example of when attackers lose control.
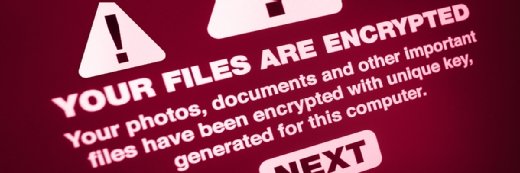
The UK and US have blamed WannaCry on North Korea, which, according to the NCSC, has shifted its focus from disrupting infrastructure to stealing money through various methods, including ransomware.
WannaCry is seen as part of those efforts, but the NCSC believes the malware did not behave as expected, causing disruption instead of being an effective way of collecting ransom payments.
In the UK, the biggest impact of WannaCry was on the NHS, but despite the level of disruption caused, it ranked only as a category two (C2) attack, requiring a cross-government response.
Martin reiterated the NCSC’s fairly long-standing view that the UK in all likelihood could face a major category one (C1) cyber attack of national significance by 2020.
He said the UK had been “fortunate” to avoid facing a C1 attack to date, unlike the US, France and other parts of Europe.
Publication of the interview comes a day after the UK’s army chief called for increased defence spending to help the country keep up with its adversaries, particularly in the light of the cyber threat.
Cyber attacks that target military and civilian operations are one of the biggest threats facing the country, UK defence chief of general staff Nick Carter warned in light of the fact that Russia, North Korea, Iran and China have been blamed for cyber attacks on the US and Europe in recent months.
Martin confirmed that some of these attacks were aimed at identifying vulnerabilities in infrastructure for potential future disruption, but that there had been no successful attempt to influence UK democracy.
Read more about the NCSC
- The NSC started several initiatives in its first year with the aim of using data drawn from those to drive better cyber security practices.
- The National Cyber Security Centre is unashamedly ambitious in aiming to make the UK the safest place to do business online, which chief Ciaran Martin sees as an achievable goal.
- The UK’s NCSC and NCA publish a joint report on the cyber threats facing UK businesses, outlining the best response strategies.
- The NCSC has the right pedigree to coordinate and balance the cyber security efforts of government, industry and academia, says GCHQ director Robert Hannigan.
The UK has previously indicated that it is building cyber-offensive capabilities, and while Martin said this will be an “increasing part of the UK’s security toolkit”, he pointed out that a cyber attack would not necessarily trigger a retaliatory cyber attack, but a range of responses would be considered, including sanctions.
The latest NCSC figures, to December 2017, show that in the NCSC’s first 14 months, it recorded no C1-level incidents, 34 C2-level incidents – including WannaCry – and 762 C3-level incidents, which are “major incidents” that typically involve only single organisations such as a defence contractor.
This means there has been just one C2-level incident and 178 C3-level incidents since September 2017.
While Martin said total protection is impossible, NCSC technical director Ian Levy believes a change in approach to cyber security could reduce the likelihood or impact of an attack.
In September 2017, Levy said the NCSC believes that by putting some science and data behind cyber security, it can demystify it and enable UK organisations to deploy effective and appropriate defences.
For this reason, Levy said the NCSC has begun publishing data and evidence to ensure people really understand how to conduct risk management properly. “Because in the end, cyber security is just risk management,” he said.
Lack of awareness
James Lyne, head of research and development at cyber security training organisation SANS Institute, said there is a desperate need to address a lack of awareness and training across the board in organisations throughout the UK to combat cyber threats.
“Ciaran Martin stated that when attacks get through, what organisations need to do is ‘cauterise the damage’,” he said. “This needs to go beyond technology, which can be bought, updated and deployed as a shield against attack. Instead, it needs to extend to people – the real weapon in the ongoing cyber fight. There is a reason why phishing is such a lucrative tool in the cyber criminal’s armoury. It targets the weakest link in the chain – humans.”
According to Lyne, organisations need to be looking at the correct training of every employee to respond better to, and stamp out, the impacts of attack on an organisation. “This means cyber security will no longer be the realm of IT departments,” he said. “All employees, including the C-suite through to HR and the wider workforce, will be required to know how to prevent hackers from penetrating the corporate network. Investing in people takes time, but it is time well spent.”
While education will never be the absolute cure, Lyne said it will stem the tide of breaches and cyber incidents that have plagued the digital age. “We need to start taking cyber security more seriously, and ensure we are equipping our current and future workforces – tapping into talent old and young, regardless of gender, to help present a united front online,” he said. “Cyber criminals will not, and do not, make exceptions for those they target, and organisations of every level should not do the same with those they train.”