Telcos could face huge fines under new security laws
Government boasts of unprecedented powers to boost the security standards of the UK’s critical national infrastructure
Telecoms companies that run foul of proposed new security legislation face fines of up to 10% of their annual turnover, or £100,000 a day, under a new law to be laid in Parliament that awards the government “unprecedented” powers to boost the security standards of the UK’s telecoms networks and force the removal of high-risk suppliers, such as Huawei.
If passed, the Telecommunications (Security) Bill will impose new duties on telecoms firms to increase the security of the networks they operate within the UK, and new responsibilities on Ofcom to monitor and assess the security of operators.
“We are investing billions to roll out 5G and gigabit broadband across the country, but the benefits can only be realised if we have full confidence in the security and resilience of our networks,” said digital minister Oliver Dowden.
“This groundbreaking bill will give the UK one of the toughest telecoms security regimes in the world and allow us to take the action necessary to protect our networks.”
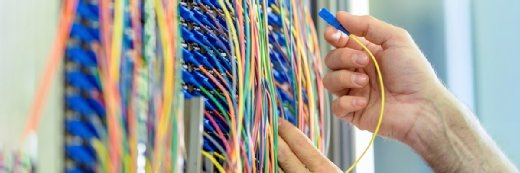
The government said its bill will strengthen the cyber security framework for technology used in both 5G and full-fibre broadband networks, including the hardware and software used at cellular masts and in telephone exchanges, a significant step in protecting the UK from hostile cyber activity by state actors.
It gives Westminster the power to direct public telecoms providers to manage high-risk suppliers, imposing controls on their use of goods, services or facilities supplied by them. It has already imposed a ban on the purchase of new Huawei equipment from the end of 2020, and enforced a commitment to remove all Huawei equipment from 5G mobile networks by 2027. The bill creates the powers that will enable the government to enshrine these steps in law and manage risk from any other suppliers in future.
It will also give the government powers to strengthen the overarching legal duties on telecoms network providers to incentivise them to prioritise cyber security – currently they set these standards themselves.
These duties will be set out in the bill, subject to consultation, but are likely to mean telcos that will need to adopt minimum security standards to their networks and services and limit the damage of any breaches that take place.
Read more about network security
- A key component of a software-defined perimeter requires client authentication before connection, while also making a network’s internals invisible to outsiders.
- Security by design incorporates security and risk management directly into network architecture, using segmentation and Agile infrastructure design.
- There are many methods available to authenticate users requesting access to an organisation’s systems. Test your knowledge with this quiz on authentication in network security.
They could include provisions to securely design, built and maintain sensitive equipment held at the core of the network, to reduce the risk of third-party equipment being a vector in a cyber attack, to control access permissions at both the physical network core and the software layer, to carry out security audits and put governance in place to better understand the risk environment, and to keep networks running freely for users while ensuring confidential data is secured when crossing them.
Ofcom, meanwhile, will be charged with monitoring and policing this new environment, and enforcing compliance.
National Cyber Security Centre technical director Ian Levy commented: “The roll-out of 5G and gigabit broadband presents great opportunities for the UK, but as we benefit from these, we need to improve security in our national networks and operators need to know what is expected of them.
“We are committed to driving up standards and this bill imposes new telecoms security requirements, which will help operators make better risk-management decisions.”