zephyr_p - stock.adobe.com
Insurance firm Chubb may be latest Maze ransomware victim
Maze ransomware group claims to have stolen personal data from the systems of cyber security insurance firm Chubb
Cyber security insurance firm Chubb is investigating a cyber security incident that may involve the Maze ransomware group. This comes after the cyber criminals behind a spate of recent ransomware attacks published a statement on their own news website claiming it has successfully attacked the organisation.
Chubb offers security insurance services covering business interruptions due to attack or error, data loss and restoration, incident response and investigation costs, crisis communications, liability from data protection failures and unauthorised networks, blackmail and regulatory investigation expenses, among other things.
In its statement, the Maze group said it had compromised Chubb's systems and said that "proofs" of this would be coming soon. It has allegedly threatened to release personally identifiable information (PII) if Chubb does not meet its demands.
A Chubb spokesperson told Computer Weekly: “We are currently investigating a computer security incident that may involve unauthorised access to data held by a third-party service provider. We are working with law enforcement and a leading cyber security firm as part of our investigation.
“We have no evidence that the incident affected Chubb’s network. Our network remains fully operational and we continue to service all policyholder needs, including claims. Securing the data entrusted to Chubb is a top priority for us. We will provide further information as appropriate.”
If confirmed as a Maze ransomware incident, this will be the latest in a string of cyber attacks conducted by the criminal group behind it. Earlier in March, the group attacked the systems of Hammersmith Medicines Research (HMR) and published the data of drug trial participants, breaking a ‘promise’ they had made not to attack any medical organisations during the Covid-19 coronavirus pandemic.
Sam Roguine, director of solutions marketing and enablement at data protection specialist Arcserve, said the attack demonstrated how even those who are acutely aware of the impact of cyber crime can still fall victim to a well-targeted attack.
“With hackers like the Maze ransomware gang publishing victims’ data online if they don’t pay a ransom, organisations must now treat all attacks like a data breach, and ensure they’re following proper compliance protocols for notifying affected customers and employees. Paying up might seem like the only option in these situations, but it isn’t – and it actually encourages more attacks,” said Roguine.
“Companies shouldn’t abandon their disaster recovery plan, and now need to be thinking of new ways they can protect stored data and backups from being extracted and used against them.
“Backup and continuous availability technologies can help mitigate the impact of an attack and should be included in this plan; by allowing organisations to spin up copies of encrypted data and systems, these solutions can help minimise downtime and prevent data loss.
“Businesses should also apply the same level of security on data backups as they do on the rest of the end points on their network, and put them on a separate domain so they’re harder for cyber criminals to reach,” he said.
Darren Wray, chief technology officer (CTO) at data privacy firm Guardum, added: “Viral ransomware is a particular nasty approach that has proven successful for a number of groups, this is made all the worse by attackers extracting data to make public.
“All firms need to be learning from such attacks and taking the risks very seriously, particularly those in high-profile sectors such as insurance companies, which are targeted because they are rich and not particularly well liked.
“These steps should include having the right processes, procedures and practises in place for new and evolving scenarios. This includes making sure that personal and commercial information is protected and, where appropriate, redacted to ensure that even if documents are stolen and exfiltrated out of the building that they are of limited use to any attacker,” said Wray.
However, despite Chubb’s security expertise, there are some troubling indications that the firm may not have taken adequate precautions to safeguard its own systems. According to Bad Packets’ Troy Mursch, scans for CVE-2019-19781, also known as “Shitrix”, found that Chubb had five vulnerable Citrix NetScaler servers.
Lost in the Maze
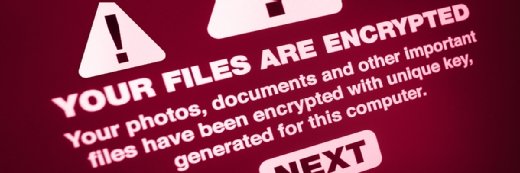
The Maze ransomware, which is believed to originate in Russia and has also gone by the name ChaCha, was first spotted in the wild in May 2019. Like other ransomware strains, it encrypts all files that it can in an infected system and demands a ransom to recover them, with the threat that the user’s data will be released onto the internet if the victim does not comply.
According to McAfee’s Alexandre Mundo, Maze was one of the first ransomware strains to make this threat, and this behaviour is now becoming much more widespread – notably being seen in infections by Sodinokibi, Nemty, Clop and a number of other ransomwares.
Threatening to release data is becoming a preferred way for cyber criminals to extort money from their victims, who – due to increasing levels of protection, off-site backups and security insurance – are becoming more reluctant to pay to have their data decrypted.
The Maze group is highly active on social media and often makes a show out of baiting and trolling prominent threat researchers with barbs such as: “You need to know that we love you researchers without you our job also would be f***ing boring as hell”.
This would suggest the group has a certain amount of influence in underground circles, and Mundo suggested that the people responsible may have day jobs in the cyber security industry, perhaps even as researchers.
The Maze ransomware itself is a sophisticated and complex piece of software that is usually packed as a .exe or .dll file. It uses a number of tricks to frustrate analysis and investigation, which are detailed in Mundo’s blog post.
“Maze is a ransomware created by skilled developers. It uses a lot of tricks to make analysis very complex by disabling disassemblers and using pseudocode plugins,” said Mundo.
“It poses a big problem to individuals and enterprises that do not pay as the developers threaten to release the information if they do not receive payment, and they do indeed keep their word on that. More and more ransomwares are exhibiting the same behaviour and we expect to see more of it this year and perhaps further into the future too.”
Read more about ransomware
- Following a swathe of high-profile ransomware attacks, the UK’s National Cyber Security Centre has made changes to its guidance, emphasising the importance of offline backups.
- By subverting kernel memory settings in Windows 7, Windows 8 and Windows 10, the RobbinHood ransomware can now delete cyber security defences from target systems.
- An apparent ransomware attack has compromised some IT and email systems at Danish facilities firm ISS World.