Tierney - stock.adobe.com
Take responsibility for cyber security basics, urges NCSC CEO
At the launch of its third annual review, NCSC head Ciaran Martin appealed for individuals and businesses to address the fundamentals of cyber security hygiene to help lighten the load
National Cyber Security Centre (NCSC) CEO Ciaran Martin has urged both individuals and businesses to shoulder their share of the burden when it comes to cyber security, addressing the basics so that government expertise and funding can be channelled into the most severe threats to the UK’s national security.
Speaking at the launch of the NCSC’s third annual review, described as its “most substantive and substantial” yet, Martin praised a “three-year record of strong, practical success” at the NCSC, whether that was through its work in stopping over a million credit cards from being used fraudulently, exposing Russian-backed cyber attacks disguised as Iranian ones, protecting critical government organisation networks from millions of suspect connections every month, or directly working with small businesses to shore up their defences, the NCSC is “delivering for the UK”.
“But there’s a part two,” said Martin. “Some attackers are still doing the same things over and over again, and too often, they’re getting through.
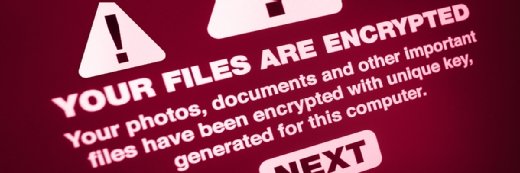
“There are things you and I can do as individuals, and that organisational leaders can do, to get ahead of the problem. All of us can use sensible, practical measures, such as better passwords, two-factor authentication and backups, and more organisations can scan for vulnerabilities and fix them, and have strategies to counter phishing attacks.
“Do that, and so much of the problem goes away and we can focus on the big challenges of the future,” said Martin.
During the third year of its life, the NCSC handled 658 major cyber security incidents, supported almost 900 victim organisations, produced 154 threat assessments, and took down almost 180,000 phishing URLs.
It also added more than 5,000 new members into its Cyber Security Information Sharing Partnership, and awarded over 14,000 Cyber Essentials certificates.
Read more about the work of the NCSC
- A group called Turla with suspected links to the Russian government stole Iranian tools and infrastructure to obscure the origins of attacks on multiple other countries, according to new evidence from the NCSC.
- As hundreds of thousands of students prepare for the new academic year, the NCSC has warned universities that they are at high risk of cyber attack.
- The UK’s cyber security agency has called out Microsoft for seriously undermining global email security by failing to provide crucial reports from its email platforms.
On cyber security skills, the past 12 months saw the NCSC deliver cyber security awareness and training sessions to 2,700 charity organisations, help 2,886 small businesses to do their own cyber security exercise simulations, engage with 2,614 students through its CyberFirst courses at universities including Bristol, Imperial College London, Leicester, Queen’s Belfast, Southampton and Warwick, and challenge nearly 12,000 girls in its CyberFirst Girls contest.
“In GCHQ’s centenary year, this is something any leader would be proud of, but of course, we cannot stand still,” said Martin. “There are too many incidents causing too much harm. We do need to get those basics right, but we do need to look at what challenges are ahead, and there are some real opportunities here to get ahead of the problem.
“We need to focus, as a national organisation, on protecting what matters most to the UK, that critical infrastructure, hard and soft. As talk of an election grows ever louder we are ready to work with the political parties, local government, the media and wider society to protect that most valuable of national commodities – our free and fair democratic system.”
Besides headline issues such as the possibility of interference or malfeasance in UK elections, such as that observed during the EU referendum, Martin said that as we move into the 2020s, looking at the “ageing, bumpy, insecure” legacy systems behind critical national infrastructure and industries will become an even bigger priority, and this will be an opportunity for the UK, as well as a challenge.
“We are dealing with a legacy that I would call accidentally insecure,” he said. “Nobody in the 1990s in public policy really saw the internet coming in the way that it did. Nobody in the industry looked at security from a structural and strategic point of view. I’m struck by the quote by Vint Cerf, one of the founding fathers of the internet, saying we didn’t focus enough on how someone could intentionally wreck this system.”
Martin noted the development of the UK’s internet of things (IoT) security code of practice, developed at the NCSC and its government partners at the Department for Digital, Culture, Media and Sport (DCMS) – which heavily informed the introduction of similar European standards through ETSI as a model to introduce objective cyber security standards throughout the digital economy, helping bring security by design to other fast-moving, innovative areas such as 5G mobile network services, artificial intelligence and quantum computing.
Collaboration critical
Raj Samani, McAfee fellow and chief scientist, said the sheer number of attacks prevented by the NCSC in the past 12 months was impressive, as well as a timely demonstration of the range and scale of threats that face both businesses and consumers.
“Keeping in mind that strength often lies in numbers, the collaboration between the public and private sectors is imperative to stemming the cyber threat to the UK,” he said.
“Organisations must find the right combination of people, process and technology to effectively protect their data, detect threats, and rapidly correct targeted systems to keep cyber attackers at bay. The NCSC’s activity in tandem with this is crucial to make Britain a safer place to live, work and invest in.”
Ilia Kolochenko, founder and CEO of Immuniweb, said: “The NCSC does a laudable job with proactive, preventive and educative efforts in the cyber space. Their transparent communications with the stakeholders are likewise greatly beneficial and serve as a decent example to other European countries.
“Security awareness and education should remain a vital part of a national cyber security strategy,” he said. “Given the rapid proliferation of technology into our daily lives with IoT and mobile technologies, everyone is a potential victim. Most of the attacks targeting UK consumers and businesses leverage some trickery and can be effectively prevented by non-technical means.”