
Rawpixel.com - Fotolia
'Serious' Twitter flaw allows hackers to post on other people's accounts
A vulnerability in Twitter allows hackers to send tweets, private messages, post images or videos, and turn off security features, says British security researcher
A British security researcher has discovered a serious flaw in Twitter that allows anyone with knowledge of the vulnerability to send tweets from other users’ accounts.
Richard De Vere, from ethical hacking firm The Antisocial Engineer, told Computer Weekly he worked out how to exploit the flaw in a matter of minutes.
“This is not a complicated hack, it’s a logic flaw in code.” he said.
The flaw exposes any account that has a mobile phone number associated with it. With knowledge of that number an attacker is able to post tweets, retweet, send direct messages, or post images and videos. According to De Vere, hackers can even switch off Twitter’s two-factor authentication functionality, which means that knowledge of a user’s login and password details would enable complete control over the account.
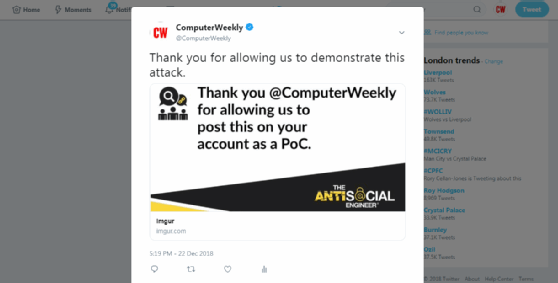
De Vere demonstrated the flaw to Computer Weekly. We shared a mobile phone number that was associated with the @computerweekly Twitter account. Within minutes, and with our written permission, De Vere posted a tweet on the account (see picture, below), which said: "Thank you for allowing us to demonstrate the attack," above an image that added, "Thank you @computerweekly for allowing us to post this on your account as a PoC [proof of concept]." We subsequently deleted the tweet.
De Vere has reported details of the flaw to HackerOne, the security testing firm that runs Twitter’s bug bounty programme for notifying vulnerabilities. He said he isn’t seeking payment but it was the only way to report the issue.
He explained to Computer Weekly in a high-level summary how the hack was possible, but asked us not to disclose this information for fear of alerting malicious actors wishing to exploit the flaw. However, De Vere said he believes some hackers may already be aware of the bug, and have used it as part of scams on Twitter where high-profile accounts appear to have tweeted promotions for fake cryptocurrency schemes.
Ed Tucker, CEO at security consultancy Byte, and a former head of IT security at HM Revenue & Customs, described the flaw as a “serious vulnerability”.
“Imagine if, say, you used 10,000 phone numbers with this vulnerability, and then wrote a tweet about something, maybe a bitcoin scam, or maybe some fake news. Then every one of those phone numbers that was associated with a Twitter account would tweet the same message,” he said.
“Imagine what you could do with that, or what has been done with that previously. You would only notice some odd behaviour on your own account maybe, and not the thousands all doing the same.”
Tucker praised The Antisocial Engineer for exposing the problem, pointing out there is no way of providing details of the bug to Twitter without going through the HackerOne reporting process.
De Vere said he expected Twitter to struggle with the problem as it could mean switching off worldwide an important part of its functionality related to the bug. But he was also confident Twitter would fix the flaw.
“Do you know how frustrating it is to actually find the solution on their own website - but it’s not enforced as standard? It’s the classic case of policy being better than real-world implementation. IT security teams are obsessed with sophisticated attacks when often social engineering just works,” he said.
Hackers have previously taken thousands of dollars in cryptocurrency scams by posing as entrepreneur Elon Musk and hijacking high-profile Twitter accounts to impersonate Musk promoting fake crypto or Bitcoin schemes.










